Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
%term
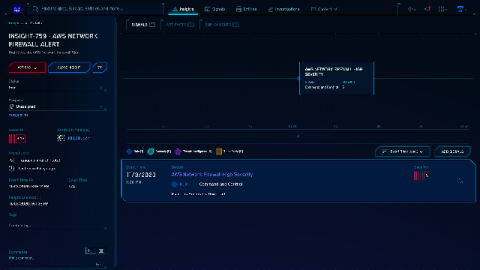
Full VPC traffic visibility with AWS Network Firewall and Sumo Logic
Pharma on the hook: cyberattackers phishing for your secret formulas
It goes without saying that mobility has become the key to productivity for any modern business. This is especially true for the highly competitive pharmaceutical industry. To be the first to bring a ground-breaking treatment or vaccine to market, pharmaceutical organizations need their employees to stay productive whether they’re working on your organization’s premises or not.
3 Ways to Prepare Your Enterprise's Data Security for a Future of Advanced Attacks
One significant negative implication of technology’s continual evolution is proportional advancement in nefarious internet activities, particularly cyber attacks. The past few years have seen a rising sophistication in cyber attacks at levels never experienced before. The worst fact is that attacks will likely only continue to get more advanced. To fight them, enterprises need to be armed with greater security tools. Legacy approaches to cybersecurity no longer cut it.
CEOs Will Be Personally Liable for Cyber-Physical Security Incidents by 2024
Digital attack attempts in industrial environments are on the rise. In February 2020, IBM X-Force reported that it had observed a 2,000% increase in the attempts by threat actors to target Industrial Control Systems (ICS) and Operational Technology (OT) assets between 2018 and 2010. This surge eclipsed the total number of attacks against organizations’ industrial environments that had occurred over the previous three years combined.
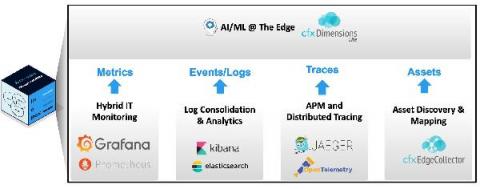
Doing AIOps Right: Addressing Monitoring Gaps with Observability-in-a-Box
Are your current expensive, traditional or legacy monitoring tool implementations holding you back? It may be time to look into Observability architectures.
Parsley Health's innovative patient care includes protecting PHI with Nightfall
Parsley Health launched in 2015 as a new approach to healthcare: a focus on holistic health with a hybrid care model of online and in-office visits. Members pay a flat monthly fee to gain access to doctors and health coaches that help manage chronic health concerns like hormonal imbalances and autoimmune disorders. With medical care including labs and doctor visits combined with lifestyle coaching and nutrition support, people can have flexible tools to maintain a healthy lifestyle.
Solving alias_method and prepend Conflicts in Our Ruby Agent
One way that we monitor API calls from within our customer’s applications is through our agent. The Bearer Agent hooks into every API call in order to read the request, read the response, and in some scenarios act upon that information. The agent replaces methods in the HTTP clients with instrumented versions that call the original methods.
The First Critical Step to Building the Modern SOC
The new Devo eBook, Building the Modern SOC, presents four evolutionary steps for creating a highly automated and efficient security operations center (SOC) that empowers analysts. This is the first in a series of blog posts that will introduce the four steps and highlight some of the most important concepts.
The First Critical Step to Building the Modern SOC
The new Devo eBook, Building the Modern SOC, presents four evolutionary steps for creating a highly automated and efficient security operations center (SOC) that empowers analysts. This is the first in a series of blog posts that will introduce the four steps and highlight some of the most important concepts.