Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Containers
Announcing Sysdig Secure 2.3: NIST + PCI image compliance checks, Kubernetes and Docker remediation tips, and more!
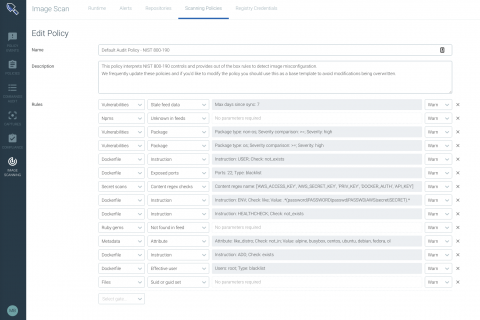
Today we are very excited to announce our latest release — Sysdig Secure 2.3! In this version of Sysdig Secure, we have invested heavily in hardening the compliance posture of Kubernetes, Docker configurations, and container images. We have released a set of features that provide compliance focused image scanning, guided remediation, compliance dashboards, and more.
Top 6 Container Security Lessons from Deploying Kubernetes and Red Hat OpenShift
We recently had the opportunity to share the lessons we have learned about container security from deploying Kubernetes and OpenShift in the field. If you don’t have time to watch the full recording of our conversation, here are a few highlights.
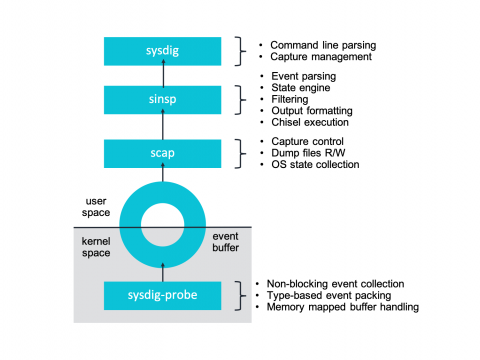
Sysdig and Falco now powered by eBPF.
At Sysdig we’ve recently undergone a pretty interesting shift in our core instrumentation technology, adapting our agent to take advantage of eBPF – a core part of the Linux kernel. Sysdig now supports eBPF as an alternative to our Sysdig kernel module-based architecture. Today we are excited to share more details about our integration and the inner workings of eBPF. To celebrate this exciting technology we’re publishing a series of articles entirely dedicated to eBPF.
Five Best Practices for Kubernetes Network Security and Compliance
Achieving network security and compliance for Kubernetes on AWS
Navigating Network Services and Policy With Helm
Deploying an application on Kubernetes can require a number of related deployment artifacts or spec files: Deployment, Service, PVCs, ConfigMaps, Service Account — to name just a few. Managing all of these resources and relating them to deployed apps can be challenging, especially when it comes to tracking changes and updates to the deployed application (actual state) and its original source (authorized or desired state).
New Tigera Secure Enterprise 2.3 Anomaly Detection Deepens Visibility into Suspicious Kubernetes Activities
Tigera is excited to announce several new capabilities with Tigera Secure Enterprise Edition 2.3, extending the ability to uncover sophisticated Kubernetes attacks. Tigera Anomaly Detection capabilities provide insight into unusual behaviors that compromise the security and performance of Kubernetes environments.
Single Sign-On for Kubernetes: An Introduction
One of the great things about Kubernetes is that it completely separates authentication and authorization. Authentication (Authn) meaning the act of identifying who the user is and authorization (Authz) meaning the act of working out if they’re allowed to perform some action. This can be thought of in terms of a Passport and a Visa.
Sysdig and IBM to collaborate on IBM Cloud Private & IBM Multicloud Manager container monitoring and security
Today at Think 2019 we’re announcing our intent to work with IBM to support the Sysdig Cloud-Native Intelligence Platform on IBM Cloud Private and IBM Multicloud Manager. By supporting IBM Multicloud Manager and IBM Cloud Private, Sysdig will help IBM customers accelerate the transition to cloud architectures.