Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Containers
8 Emerging Trends in Container Orchestration
Enforce Docker Image CIS Policy Compliance with Tripwire for DevOps
We are working hard adding features to our new Tripwire for DevOps service, initially announced at BlackHat 2018. If you are a loyal State of Security follower, last you read we added Auditing for Amazon Machine Images (aka AMIs). Today, we are introducing CIS policy compliance auditing for Docker images. Tripwire for DevOps allows you to evaluate your Docker Images to check for policy compliance at build time.
Clarifying the Misconceptions: Monitoring and Auditing for Container Security
An effective container security strategy consists of many parts. Organizations should first secure the build environment using secure code control along with build tools and controllers. Next, they should secure the contents of their containers using container validation, code analysis and security unit tests. Finally, they should develop a plan to protect their containers in production systems by focusing on runtime security, platform security and orchestration manager security.
Best Practices for Running Containers in Production.
8 Surprising Facts About Real Docker Adoption
Achieving Simplicity and Scale for Your Application Connectivity Infrastructure
Complete Guide to Container Security
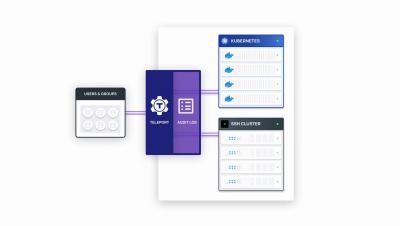
Teleport 3.0 Demo
Strengthen Production Systems with Container Runtime Security
Container security is not a unitary action but a multifaceted process. It involves securing the build environment using secure code control and other strategies. The procedure also necessitates securing containers’ contents via code analysis and unit tests.