Collect Evidence & Artifacts from people with Request Links
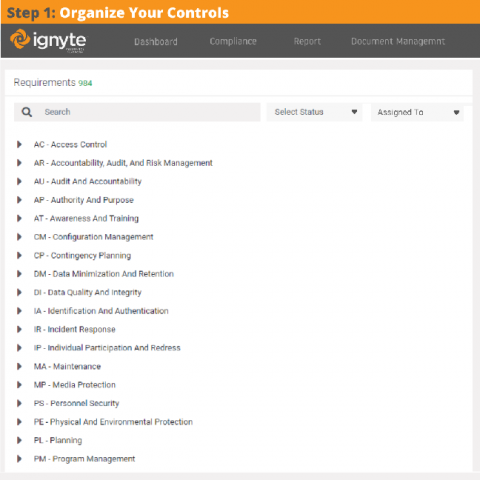
Controls management and assessments are critical for properly managing a complete information security program. Similarly, evidence collection, management, and approval is vital for proper control based security governance programs in any organization.