Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Security
Cybersecurity sketchnotes with Gavin Ashton: Evolution of the attack surface
DevSecOps in Practice: How to Embed Security into the DevOps Lifecycle
You’ve heard of DevOps. And by now, you’ve probably also heard of DevSecOps, which extends DevOps principles into the realm of security. In DevSecOps, security breaks out of its “silo” and becomes a core part of the DevOps lifecycle. That, at least, is the theory behind DevSecOps. What’s often more challenging for developers to figure out is how to apply DevSecOps in practice. Which tools and processes actually operationalize DevSecOps?
Lookout Partners with Telkomsel to Deliver Mobile Device and Application Security
Mobile devices and mobile apps have become a primary way for most of us to get work done and manage our lives. This is why I’m excited that Telkomsel has partnered with Lookout to launch Telkomsel Mobile Endpoint Protection (MEP) and Telkomsel Mobile App Protection (MAP). These solutions are powered by the cloud-delivered Lookout Security Graph.
6 Cybersecurity Tips for Working from Home
Here at Tripwire, we, like many others, recently surpassed the one-year anniversary of working from home due to the COVID-19 pandemic. Since March of 2020, we have converted kitchens, spare bedrooms and garages into office spaces. Our pets and children have become our coworkers, and companies are reporting a sudden increase in shirt sales as opposed to pant sales.
SC Awards 2021: Redscan a finalist in three categories
Agentless Monitoring with Tripwire Enterprise: What You Need to Know
As we know, Tripwire Enterprise (TE) is the de-facto go-to solution for File Integrity Monitoring (FIM). In normal operations, we deploy a TE agent to a system we want to monitor. TE then uses that agent to baseline the system against the appropriate rules, creating a known good state for that system. Moving forward, that system is monitored for change per the rules that were used to create the baseline.
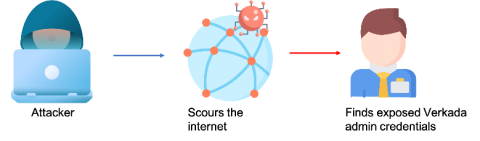
Operation panopticon: How a weak IAM strategy led to the security camera hack across organizations
On March 9, 2021, Verkada, a software company that specializes in making security cameras for monitoring physical access control, was subject to a security hack. Hackers gained access to the video feed of at least 15 thousand cameras deployed across various locations and exposed the inner workings of hospitals, clinics, and mental health institutions; banks; police departments; prisons; schools; and companies like Tesla and Cloudflare.
Considerations for performing IoMT Risk Assessments
Internet of Medical Things (IoMT) products refer to a combination of medical applications and devices connected to healthcare information technology systems through an online computer network or a wireless network. IoMT devices rely heavily on biosensors, critical in detecting an individual's tissue, respiratory, and blood characteristics. Non-bio sensors are also used to measure other patient characteristics such as heart and muscle electrical activity, motion, and body temperature.
What is cyber security architecture? Elements, purpose and benefits
The principles of cyber security architecture are indeed similar to IT architecture. Networks are only going to expand, technology is going to evolve, and one constant question on every organisation’s mind is “How to ensure the protection of our assets?”. This concern is further heightened in companies whose services are mainly digitised, accounting for over 60% of UK businesses.