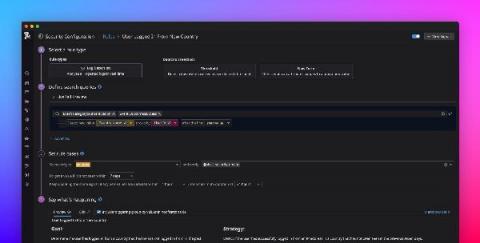
Detect anomalous activity in your environment with new term-based Detection Rules
When it comes to securing your production environment, it’s essential that your security teams are able to detect any suspicious activity before it becomes a more serious threat. While detecting clear-cut attacker techniques is essential, being able to spot unknowns is vital for full security coverage.