Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Security
CVE-2022-20842 & CVE-2022-20827 - Critical Vulnerabilities in Cisco Small Business Routers
1Password named one of Forbes Cloud 100
We’re thrilled to announce that 1Password has been included in the Forbes 2022 Cloud 100, the definitive ranking of the top 100 private cloud companies in the world!
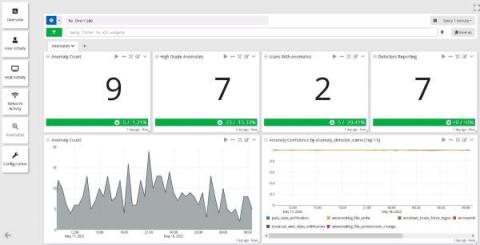
Graylog Security Anomaly Detection: Metrics Ease the Workload
Cybersecurity Expert Interview: Whitney Champion
My name is Whitney Champion and I'm the lead architect and one of the co-founders of Recon InfoSec. Basically I'm responsible for building and maintaining our security stack, our applications, and also our training platform: The Network Defense Range, or NDR. We're a managed security services provider, and we're based out of Austin, Texas. There are roughly 15 of us and we provide managed detection and response services and training.
3 Configurations to Improve Slack Monitoring
With over 200% YoY Growth and used by 100,000+ Organizations globally, Slack has become an indispensable internal communication tool for teams to coordinate their activities. But when it comes to exchanging information and external sources, certain risks are at play that requires more insight and attention. Slack links to various vital systems within many organizations, making it an easy, central access point hackers can use to reach multiple systems.
The Increase in Ransomware Attacks on Local Governments - What Makes Public Sector Organizations Vulnerable to Ransomware?
In Spring 2022, Lincoln College announced that it would permanently close on May 13 and noted that a December 2021 ransomware attack had contributed to its closure.
Detect cryptojacking with Sysdig's high-precision machine learning
Is cryptojacking draining your resources and exposing your organization to financial and reputation damage risk? The rise in cryptojacking, which is an illegal form of mining cryptocurrency by the unauthorized use of someone’s computing resources, has reached alarming levels. According to the Google Threat Horizon report, 86% of compromised cloud instances in 2021 were used for cryptomining. That paints the picture quite clearly.
Cryptominer detection: a Machine Learning approach
Cryptominers are one of the main cloud threats today. Miner attacks are low risk, low effort, and high reward for a financially motivated attacker. Moreover, this kind of malware can pass unnoticed because, with proper evasive techniques, they may not disrupt a company’s business operations. Given all the possible elusive strategies, detecting cryptominers is a complex task, but machine learning could help to develop a robust detection algorithm.
Controlling your server with a reverse shell attack
Creating and running an application in your favorite language is usually pretty simple. After you create your application, deploying it and showing it to the world is also quite straightforward. The last thing you need is someone to take over your system and fully control your brand new application. In this article, I’ll explain how this can happen with a reverse shell attack. Note that the code examples in this article are for educational purposes only.