Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Security
Zero trust in the cloud: Best practices and potential pitfalls
Architecturally speaking, cloud-native applications are broken down into smaller components that are highly dynamic, distributed, and ephemeral. Because each of these components is communicating with other components inside or outside the cluster, this architecture introduces new attack vectors that are difficult to protect against using a traditional perimeter-based approach.
Node.js multithreading with worker threads series: worker_threads tutorial
Node.js provides a single-threaded JavaScript run-time surface that prevents code from running multiple operations in parallel. If your application typically employs synchronous execution, you may encounter blocks during long-running operations. However, Node.js itself is a multi-threaded application. This is evident when you use one of the standard library’s asynchronous methods to perform I/O operations, such as reading a file or making a network request.
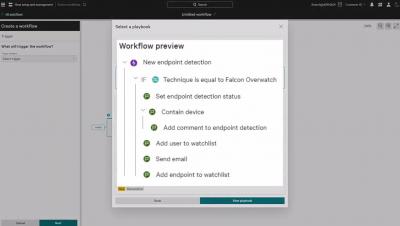
Create Automated Workflows with Pre-Built Falcon Fusion Playbooks
Cybersecurity Awareness Month: Prioritizing Patching
Top 3 SIEM challenges in multi-cloud environments
A Day in the Life of an Ethical Hacker: Q&A With Professional Hacker Agne Marija Bucyte
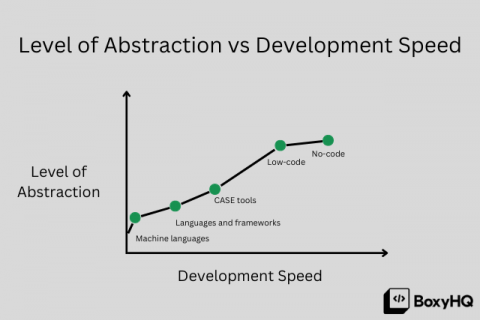
How low-code solutions are changing how we build products and workflows
We have all heard the terms low-code or no-code being thrown around as buzzwords over the last few years but what does this mean and how is it changing the way businesses and individuals solve problems? I am going to use our product SAML Jackson to explain how low-code solutions are changing the way we build products.
Forward Networks Named to Department of Homeland Security's Continuous Diagnostics and Mitigation Program's Approved Product List
Amid real estate volatility, cybercriminals are profiting
It is easy to think of cybercrime as a phenomenon only impacting the digital space. However, as trends are showing, digital attacks have a very real and very physical impact. According to the FBI, there has been a surge in rental and real estate property scams conducted via digital means, whether that’s the insertion of rogue actors into the property purchase chain, or hijacking of legitimate websites to promote false, money scamming listings.