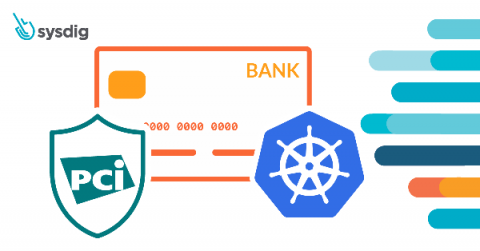
Uncovering Bots in eCommerce Part One: Carding
No one wants to be a victim of payment card fraud, yet more of us are falling foul to the myriad of techniques used by hackers to steal payment card information and use it for their own gain. To mitigate this malicious activity, it is vital that eCommerce sites apply security measures that protect consumers and sellers alike from carding and other major bot threats.