Event Log Management for Security and Compliance
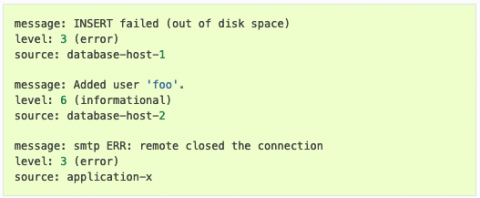
Security log management is the process of collecting, storing, and correlating the network data that details all activity in your systems and networks. Every action in an organization’s network generates event data, including records produced by operating systems, applications, devices, and users. The Center for Internet Security (CIS) identifies log management as a basic control for detecting malicious actors and software hiding in networks and on machines.