Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Product Release
Use Snyk security policies to prioritize fixes more efficiently
Snyk security policies just got a whole lot more powerful with a new action and two new conditions, helping your development and security teams assess risk and focus resources more efficiently. For developers, the less “noise” the better. Tasked with fixing issues that are simply not important or relevant is a waste of valuable development time and will likely result in creating frustration and mistrust.
Kubernetes version 1.22 release - everything you should know
Kubernetes version 1.22, the latest release of Kubernetes, comes with bug fixes, enhancements, and new features that make the platform more stable, scalable, and user-friendly. There are a total of 56 improvements with different maturity levels and a considerable number of API removals. In this article, I’ll focus on the security-related changes in Kubernetes as well as a few other significant changes in Kubernetes API and usability.
Product Update: Detectify fuzzing engine will cover public-facing APIs
Detectify is expanding its web app fuzzing engine to scan public-facing APIs for vulnerabilities. Earlier in the year, we released a new fuzzing engine, and it was developed with API scanning in mind. In Fall 2021, we will roll out open beta testing. You can register for Detectify API fuzzer updates and beta testing program.
Elastic 7.14.0 introduces the industry's first free and open Limitless XDR
We are pleased to announce the general availability (GA) of Elastic 7.14, including our Elastic Enterprise Search, Observability, and Security solutions, which are built into the Elastic Stack — Elasticsearch and Kibana. Elastic 7.14 empowers organizations with the first free and open Limitless XDR, which delivers unified SIEM and endpoint security capabilities in one platform.
Snyk Code adds security scanning for C# and .NET
As a quick note, I have a personal history with .NET, including time working at Microsoft as a .NET evangelist. And I’ve briefly met Anders Jejlsberg, the designer of C# and Typescript, so this blog is a bit personal for me. We are happy to announce that Snyk Code scans for security vulnerabilities and provides remediation suggestions for yet another language: C#. This adds a major language to our portfolio which includes support for Java, JavaScript, TypeScript, and Python.
Announcing Social Trends: Use social media for security intelligence
We are excited to announce the availability of Social Trends, adding social media intelligence (SOCMINT) to Snyk’s vulnerability data to help development and security teams prioritize vulnerabilities more effectively. Given the size of vulnerability backlogs facing organizations today, finding and fixing security vulnerabilities in a timely manner is a monumental task. There simply are not enough hands on deck to triage and tackle all the vulnerabilities on the list.
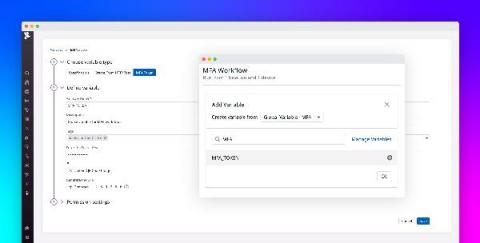
Introducing multi-factor authentication in Datadog Synthetic tests
Multi-factor authentication (MFA) is an increasingly popular method for securing user accounts that requires users to provide two or more pieces of identifying information when logging into an application. This information can consist of unique verification links or codes sent to the user’s phone or email address, as well as time-based one-time passwords (TOTPs) generated by authenticator applications or hardware.
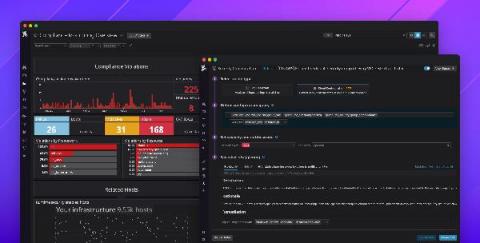
Introducing Datadog Cloud Security Posture Management
Governance, risk, and compliance (GRC) are major inhibitors for organizations moving to the cloud—and for good reason. Cloud environments are complex, and even a single misconfigured security group can result in a serious data breach. In fact, misconfigurations were the leading cause of cloud security breaches in 2020. This puts a lot of pressure on developer and operations teams to properly secure their services and maintain regulatory compliance.
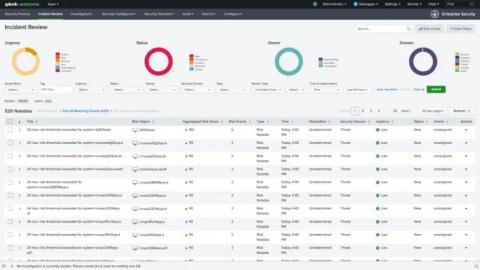
What's New with Splunk Enterprise Security 6.6?
We are super excited to announce updates to Splunk Enterprise Security (ES) with our latest 6.6 release. Get ready for the latest and greatest that Splunk Enterprise Security has to offer. Let's dive right into it.