The Biggest Security Nightmares from 2023 and How They Could Ruin Your 2024
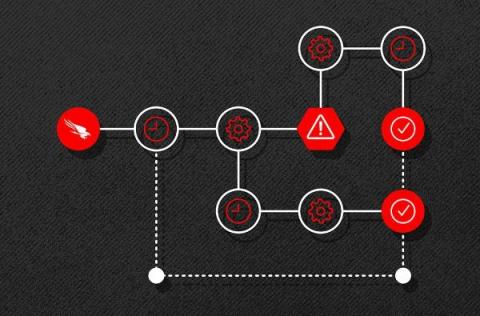
It feels like the number of security issues affecting vital internet-exposed assets is never-ending. No one can predict the next big vulnerability. But exposure management techniques can help prepare your organization for a wide range of issues by identifying, validating, and mobilizing your response to emerging threats. These processes also include validating fixes and issues, a well-documented mobilization process, and automatic scanning for high value assets.