Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest News
How Hackers Target Small Businesses - and How to Protect Yourself
It's important to understand how hackers target small businesses and that smaller companies are a favorite object of hackers. Why? Because small businesses often lack the security measures and financial resources in place that larger businesses have.
Code Intelligence Raises $12M for Dev-First Security
We are thrilled to announce that we secured our Series A funding round of $12 Million to fulfill our vision of a world where security is a given, not a hope. The round was led by US-based Tola Capital and introduced experienced business angels such as Thomas Dohmke. We will use the funds to add support for more programming languages, provide further dev tool integrations and grow the team.
The role of attack surface management to bolster data breach protection
The attack surface is an organization’s digital exposure that an attacker could exploit to get unauthorized access to a system and extract data or other sensitive information. It could also be used as a point within a chain of attacks. As Organizations increasingly rely on SaaS services and products, the digital attack surface is more than the firewall and network.
New Black Basta Ransomware Group
The Era of Automated SAST has Begun
For consecutive years, applications have remained the top attack vector for black hats, with supply chain attacks not far behind. At the same time, market research indicates that enterprise security managers and software developers continue to complain that their application security tools are cumbersome. When asked, many developers admit that they don’t run security tests as often as they should, and they push code to production even when they know it has security flaws.
Trustwave MDR, DbProtect and MailMarshal Named Finalists for SC Media and SC Europe Awards
SC Media and SC Media Europe have named Trustwave as a finalist for several awards to be announced this summer. SC Media Europe has shortlisted two Trustwave products as finalists: SC Media will announce winners on Aug. 22 and SC Media Europe will announce winners on June 21. SC Media, which represents the U.S. branch of the cybersecurity publisher, has named Trustwave DbProtect as a finalist in the Best Database Security Solution category.
Top 5 E-Commerce Cybersecurity Trends For 2022 That You Need To Know
Cyberattacks on e-commerce sites are always a frequent phenomenon. Every e-commerce retailer wants to improve the consumer experience, but if they're not careful, their efforts could transform their business website into a playground for cybercriminals. Without a doubt, they are gold mines of personal and financial information for threat actors. And as a result, companies worldwide are losing billions to e-commerce fraud (more than 20$ billion in 2021).
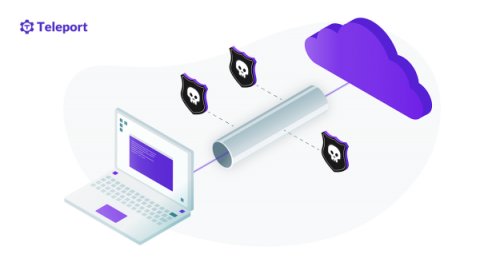
What is a VPN? Types of VPNs and How They Work
As the number of remote workers grows, virtual private networks (VPNs) are becoming a popular way to grant remote access to employees while hiding online activities from attackers. With a VPN, your organization can secure network traffic between your site and users by creating an end-to-end secure private network connection over a public network. In this article, you will learn how a VPN works, what protocols are needed, what challenges are involved, and what alternatives are available.
A Hospital's Cybersecurity: 10 Steps to Help Ensure Patient Safety and Continuous Operations
Across a health system’s digital terrain, the most vulnerable assets are connected medical devices. If those devices become compromised, the infiltration could impact a patient’s privacy, health and safety. Moreover, it could shut down care delivery for days, weeks or longer, with long-lasting financial and reputational impacts. According to Deloitte, an estimated 70% of medical devices will be connected by 2023.