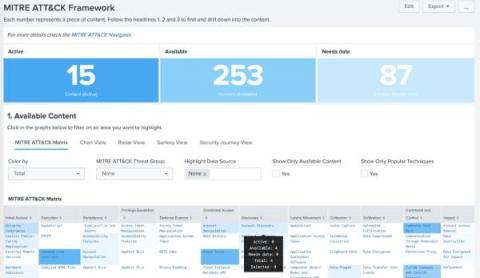
'One-Stop Shop' Functionality with Global Search
There are many critical factors to ensuring an effective cybersecurity program; however, two of the most important are accuracy and timeliness. With limited search capabilities that direct you to insufficient results or extended navigation time to find items of relevance, the cyber risk of your rapidly growing vendor ecosystem is left unmanaged. Think about it like this: when you have two contacts in your phone saved under the same first name, how do you determine which one is the right one to call?