Red Team: O365 MFA Bypass To Device Compromise
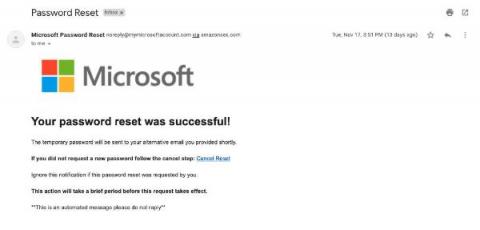
The array of phishing vectors used by attackers is constantly expanding. On a daily basis we observe numerous different phishing themes such as voicemails, fake invoices and documents requiring signing. Recently, we have seen more topical themes such as US elections, COVID-19 and Brexit.