Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest News
The IaC Showdown: Terraform vs. Ansible
Infrastructure as code (IaC) has become the de-facto method for dealing with infrastructure at scale. This codification of infrastructure configurations lets software development teams create version-controlled, reusable configurations. Moreover, it enables integrating infrastructure management as a part of the delivery pipeline.
Ekran System Provides New Report Customization Opportunities for Microsoft Power BI Users
MSP Summit Highlights Growth Potential for Channel Partners
Cyber breaches are everywhere, people are working from anywhere, and data creation is exploding. As a result, businesses want solutions that make data collaboration and governance easier and more secure, and MSPs are at the forefront of this market opportunity. Those opportunities were on full display last week as more than 250 managed service providers, technologists, and Egnyte leaders met virtually—and in-person in London—for Egnyte’s annual MSP Summit.
What makes evidence uniquely valuable?
American novelist F. Scott Fitzgerald famously wrote that “the test of a first-rate intelligence is the ability to hold two opposing ideas in mind at the same time, and still retain the ability to function.” All experienced security practitioners learn to master this mental trick. On the one hand, they believe efforts to prevent and detect breaches will be effective. On the other hand, they diligently prepare for the day when their efforts will fail.
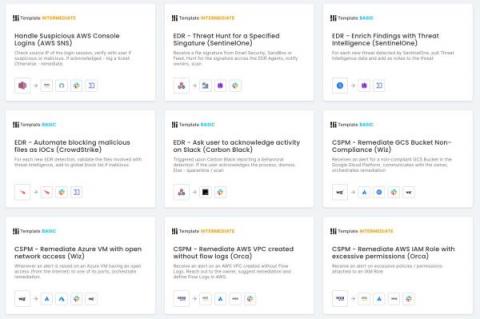
Latest Features Enhance Workflow Creation, Add Modern Controls
The consensus on the state of cybersecurity professionals tends to fall somewhere between “burdened by high volumes of responsibility” and “dangerously understaffed and suffering from unhealthy levels of stress,” depending on how optimistic your source is.
Q1 2022 Threat Landscape: Threat Actors Target Email for Access and Extortion
In Q1 2022, Kroll observed a 54% increase in phishing attacks being used for initial access in comparison with Q4 2021. Email compromise and ransomware were the two most common threat incident types, highlighting the integral part played by end users in the intrusion lifecycle.
Everything You Need to Know to Prevent JavaScript Supply Chain Attacks
JavaScript supply chain attacks are a bit like rolling thunder. The boom starts in one location and then reverberates along a path, startling folks, shaking windows, and—if there is a significant enough storm to accompany the thunder—leaving varying degrees of devastation in its wake.
5 Historic Third Party Breaches
Third-party data breaches are one of the most concerning issues in cybersecurity today. You need your third parties to do business, but you can’t always trust (or verify) that their cybersecurity controls are as strong as they say, no matter how many questionnaires you send out. And of course, cybercriminals know that by hitting vendors rather than every single company separately, they can get the most ill-gotten gains for their effort.
Webinar: Outsourced Cybersecurity or In-House? How to Choose the Best Approach for Your Organization
The coronavirus pandemic created new challenges for businesses as they adapt to an operating model in which working from home has become the ‘new normal. In addition, threat actors constantly change their strategies, tools, and techniques. When their attacks become less effective, they look for new weaknesses to expose and move to.