Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest News
Elastic Security 8.1: Stop novel attacks in their tracks
With the release of Elastic Security 8.1, enhance defenses against novel attacks like Log4Shell and prevent adversaries from compromising macOS systems. Achieve visibility into host-based network activity, leverage new sources of threat intelligence, collect data from across your enterprise, and more. Let’s jump in.
Cloud Threats Memo: Tightening Up Leaky GitHub Repositories
Another day, another cloud service leaking personal data because of a misconfiguration. And before you jump to any conclusions, no, it’s not a leaky bucket on AWS S3 or a public blob on Microsoft Azure… The culprit is, once again, GitHub, where an open-source hardware manufacturer has inadvertently left exposed a private-to-public repository that “could have enabled unauthorized access to information about certain user accounts on or before 2019.”
CVE-2022-0492: Privilege escalation vulnerability causing container escape
Linux maintainers disclosed a privilege escalation vulnerability in the Linux Kernel. The vulnerability has been issued a Common Vulnerability and Exposures ID of CVE-2022-0492 and is rated as a High (7.0) severity. The flaw occurs in cgroups permitting an attacker to escape container environments, and elevate privileges. The vulnerable code was found in the Linux Kernel’s cgroup_release_agent_write in the kernel/cgroup/cgroup-v1.c function.
Dirty Pipe: Linux Kernel Vulnerability Could Lead to Root Privileges - CVE-2022-0847
Breaking the bias in cybersecurity
Happy International Women’s Day 2022. This year the theme is 'Break the Bias,' which calls for everyone to take action and call out gender bias, discrimination, and stereotyping. Infosecurity Magazine recently highlighted 90% of security leaders are suffering skills shortages, with 3.5 million positions unfilled in 2021. According to Best Colleges, women continue to outnumber men in college completion.
Introducing the new LimaCharlie website & why it matters for security teams
We are very excited to announce the launch of the new, improved LimaCharlie website (yes, this one!). The new site allows content to load faster, and, enhanced by a polished design, reflects the level of professionalism we exemplify. Overall, the new website facilitates a clear understanding of the value proposition our product encompasses. However, these are not the only reasons why we are so excited about it.
5 Cybersecurity Tools to Safeguard your Business
With the exponential rise in cybercrimes in the last decade, cybersecurity for businesses is no longer an option — it’s a necessity. Fuelled by the forced shift to remote working due to the pandemic, US businesses saw an alarming 50% rise in reported cyber attacks per week from 2020 to 2021. Many companies still use outdated technologies, unclear policies, and understaffed cybersecurity teams to target digital attacks.
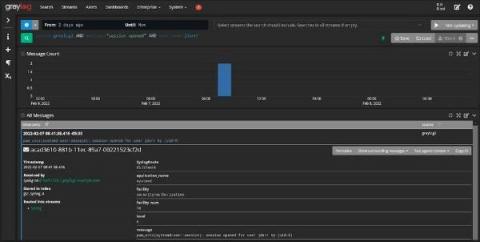
Using Centralized Log Management for ISO 27000 and ISO 27001
As you’re settling in with your Monday morning coffee, your email pings. The subject line reads, “Documentation Request.” With the internal sigh that only happens on a Monday morning when compliance is about to change your entire to-do list, you remember it’s that time of the year again. You need to pull together the documentation for your external auditor as part of your annual ISO 27000 and ISO 27001 audit.
What is Malware & How to Protect Ourselves From Computer Viruses
Do you remember when viruses used to be funny and not such a big deal? Maybe a cat would constantly pop up on your desktop or you’d get spammed with hundreds of ads for male enhancement pills? Well, the early 2000s are over (yes, it’s depressing) and malware has advanced far beyond its somewhat quirky origins. Today, viruses have become extremely sophisticated and it’s difficult to know for sure if your files have been infected or not. So what is malware exactly?