Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest News
Spotting Log4j traffic in Kubernetes environments
Editor’s note: This is the latest in a series of posts we have planned over the next several weeks where we explore topics such as network monitoring in Kubernetes, using sidecars to sniff and tunnel traffic, show a real-world example of detecting malicious traffic between containers, and more! Please subscribe to the blog, or come back for more each week.
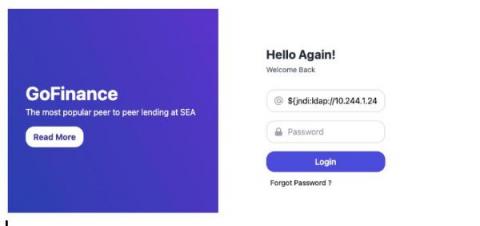
FTSE 100 credential theft study 2022
Corporate credential theft is a targeted effort and makes FTSE 100 companies credentials particularly attractive to cybercriminals with accelerated digital transformation (BYOD and hybrid working). Once an attacker gets hold of stolen user credentials and passwords, they can sell the credentials in the cybercrime underground or use them to compromise an organization’s network, bypassing security measures and threaten the credibility and integrity of the institution.
The Future of AIOps
Impact Analysis: RubyGems Critical CVE-2022-29176 Unauthorized Package Takeover
On May 6, 2022, a critical CVE was published for RubyGems, the primary packages source for the Ruby ecosystem. This vulnerability created a window of opportunity for malicious actors to take over gems that met the following criteria: Because RubyGems provides data dumps that include a lot of information, it is unfortunately relatively simple to create an automated mining process for these criteria.
What to look for in a vCISO as a service
“Approximately 64% of global CISOs were hired from another company” according to the 2021 MH Global CISO Research Report. The reasons are because of talent shortages, the role is still new to some companies, and companies have not created a succession plan to support internal promotions. To overcome these challenges, companies can look to Virtual Chief Information Security Officer (vCISO) or a vCISO as a service provider.
Municipal Cybersecurity Plan: Top 5 Factors to Incorporate
Cyber attacks on state and local governments continue to be on the rise. With more attacks targeting municipalities, there needs to be a push toward boosting cyber preparedness. Even though the risks remain at an all-time high for municipalities, the lack of budget and knowledge has caused officials to put cybersecurity on the back burner.
Newly minted filters, improvements to bulk actions, and SSL assessments
Remediating vulnerabilities efficiently is the cornerstone of a great vulnerability management program. Prioritizing becomes paramount as resources are often limited. Sometimes teams might pinpoint specific vulnerability types that are particularly risky for their attack surfaces, such as a misconfigured Amazon S3 bucket or even a new XSS vulnerability. Users can now filter the /Vulnerabilities view by title, such as a specific type of XSS or even the CVE name.
What is a Security Whitelist?
In April 2022 alone, there were 14.3m records breached due to 80 significant security incidents. These incidents make up a complex, shifting landscape of cyberattacks that require increasingly sophisticated defenses. While many of our methods are becoming more complex, some of our mechanisms are timeless, like the security whitelist. Also called an “allow list,” the security whitelist defines the permitted actions and blocks everything else.
urlscan's Johannes Gilger: How automation can free up resources and streamline security investigations
In our fourth episode of the Future of Security Operations podcast, Thomas speaks with Johannes Gilger— CEO and founder of urlscan, a URL and website scanner that enables users to take a look at the individual resources that are requested when a site is loaded. Prior to founding urlscan, Johannes managed the Threat Intelligence Automation team at CrowdStrike.