Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest News
Interactive Phishing Mark II: Messenger Chatbot Leveraged in a New Facebook-Themed Spam
Facebook Messenger is one of the most popular messaging platforms in the world, amassing 988 million monthly active users as of January 2022, according to Statista. One important feature of this platform is Messenger’s bot. Within the current digital landscape, chatbots are widely used by companies and individuals to connect with their customers online, and almost immediately pops up when chatting with brands or businesses.
5 reasons why Sysdig partners with Proofpoint to enhance cloud security
At Sysdig, we are constantly looking for ways to improve the security posture of the organizations that we work with. One of the areas we continuously improve upon is our platform’s threat intelligence and detection capabilities that leverage the open-source Falco project. We incorporate threat intelligence sourced from our own strategically placed honeypots, data collection systems, and multiple other open-source feeds.
Preventing container runtime attacks with Sysdig's Drift Control
Containers revolutionized how we build, deploy, and run applications with increased speed, agility, and scalability. But, as often happens with transformative technologies, they require an evolution to security strategy. Centralized deployments inside a protected perimeter gave way to continuous and distributed deployment of containers, creating a growing, dynamic, and distributed attack surface. IT and security teams were left blind and exposed in the cloud.
New Netskope Customer, United States Patent and Trademark Office (USPTO), Leads the Way in Security Modernization with First Ever US Federal Civilian SASE Contract
Today, Netskope announced it has been awarded, through SEWP Prime Anacapa Micro and distributor Merlin Cyber, the industry’s first Secure Access Service Edge (SASE) U.S. Federal Civilian Government contract in history, led by the United States Patent and Trademark Office (USPTO). This is a significant industry milestone as traditional, perimeter-based approaches to security will no longer work in a mandated cloud-first environment where data can be accessed from anywhere.
What is the ICT Supply Chain? Things Your Business Needs to Know
Cyber attacks and data breaches are top of mind for businesses around the world as attacks on vulnerable networks persist. It is more important than ever to ensure cyber security and resilience programs are in place for your business and third-party suppliers. The information and communications technology (ICT) supply chain is a globally-interconnected ecosystem that involves CT software, hardware, and services including suppliers, vendors, and contractors.
Modernizing Cybersecurity Through New Standards for Risk Intelligence
Leaders from the SEC, Cyber Threat Alliance, and National Association of Corporate Directors recently joined with SecurityScorecard to share their insights on the state of cybersecurity risk management today. Earlier this month, the New York Department of Financial Services (NY DFS) announced efforts to modernize their supervision process, with the creation of the Cybersecurity and Information Technology Baseline Risk Questionnaire (CIBRQ).
Do you know how to identify your third-parties', third-parties?
It might sound confusing at first, but knowing who your third parties also rely on for their day-to-day business operations is key to building out a smarter and more informed vendor risk management program. Commonly known as fourth-party concentration risk, the ability to determine the fourth-party vendors in your digital supply chain that serve a majority of your third-party vendors can help organizations avoid potentially catastrophic supply chain risk from such a dependency.
Analytics and Automation in the Autonomous SOC
SOC analysts suffer from alert fatigue caused by too many data sources and platforms, too little context in investigations, too few people, and too little time. Mature cybersecurity teams manage this challenge by leveraging an integrated set of data analytics capabilities from best-of-breed solutions to establish an end-to-end experience — from data collection to response.
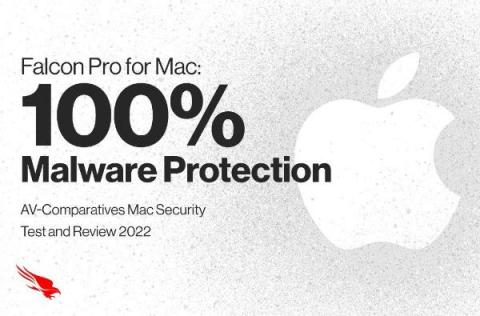
CrowdStrike Falcon Pro for Mac Achieves 100% Mac Malware Protection, Wins Fifth AV-Comparatives Approved Mac Security Product Award
CrowdStrike believes that continuous testing and evaluation by third-party organizations is critical in helping customers make informed decisions about which security solution best fits their needs. This is why CrowdStrike continues to participate in more third-party testing than any other next-gen endpoint cybersecurity vendor.