Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest News
Managing Cyber Risk in the Insurance Supply Chain
This week in London, SecurityScorecard hosted a roundtable discussion on cyber risk in the insurance supply chain. Keynote speaker Santosh Pandit, head of Cybersecurity at the Bank of England, shared his insights with 20 London-based insurers on managing cyber risk in the financial sector and the latest regulatory initiatives that may impact the insurance industry.
SecurityScorecard Identifies Infrastructure Linked to Widespread MOVEit Vulnerability Exploitation
New disclosures regarding the widespread exploitation of CVE-2023-34362, a new vulnerability affecting the MOVEit file transfer software, and the Cl0p ransomware group’s claim of responsibility for its widespread exploitation and the resulting data theft, have continued in the weeks since the vulnerability’s original publication.
3 Steps to Bridge Cyber Risk Communication Gaps
Debunking the Misconception That CRQ Requires a Lot of Data Collection
A Guide to Handling the MOVEit Attack
Last week, a vulnerability in the popular MOVEit managed file transfer service was exploited by the CL0P ransomware gang to execute data breaches – an increasingly common cybersecurity attack technique where popular software is exploited to target, by extension, their users. Victims of this hack include British Airways, Boots, BBC, and multiple US government agencies.
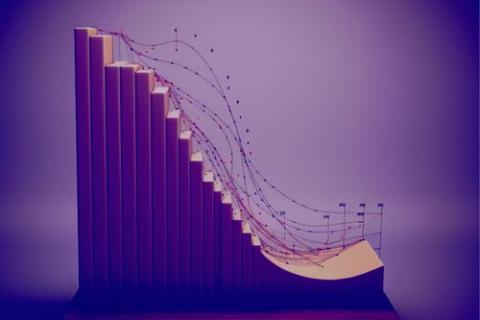
5 Effective Strategies to Mitigate Market Risk
Cybersecurity Risk Assessment Tools You Can Use Year-Round
Mend.io Launches AppSec Risk Assessment Program
At Mend.io, we’re always looking for ways to help organizations understand their application security risk. This week, we’re proud to announce a new initiative designed to make it easier than ever for organizations to visualize and remediate their biggest sources of risk: the Mend.io AppSec Risk Assessment Program.