Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
March 2022
Cyber Compliance and Data Breach Notifications
Ransomware isn’t just an internal threat for your organization, it’s also a global crime, and data breach notifications are governed by various laws, policies, and agencies. Let’s go over some common cyber-compliance questions about ransomware, data breach notification and reporting, and the laws that cover cybercrime.
Threat Update DoubleZero Destructor
The Splunk Threat Research Team is actively monitoring the emergence of new threats in the cyber domain of ongoing geopolitical events. As we have shown previously in several releases, including HermeticWiper and CaddyWiper, actors in this campaign are deploying, updating, and modifying stealthier malicious payloads. On March 17th, 2022, the Ukraine CERT discovered a new malicious payload named DoubleZero Destructor (CERT-UA #4243).
Climbing the Ransomware Maturity Curve
Vidar Malware Launcher Concealed in Help File
Appending a malicious file to an unsuspecting file format is one of the tricks our adversaries use to evade detection. Recently, we came across an interesting email campaign employing this technique to deliver the info stealer Vidar malware. First, let’s examine the email delivery mechanism, then go on to take a closer look at the Vidar malware itself. Figure 1: The malicious spam message The messages in this campaign have two things in common.
Outpost24 webinar - The State of Ransomware in 2021 and How to Limit Your Exposure
AvosLocker ransomware - what you need to know
AvosLocker is a ransomware-as-a-service (RaaS) gang that first appeared in mid-2021. It has since become notorious for its attacks targeting critical infrastructure in the United States, including the sectors of financial services, critical manufacturing, and government facilities. In March 2022, the FBI and US Treasury Department issued a warning about the attacks.
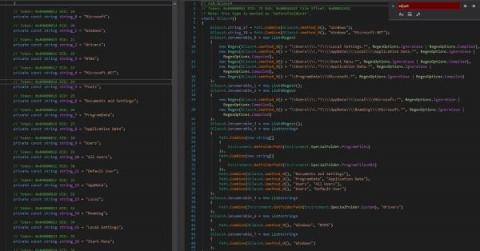
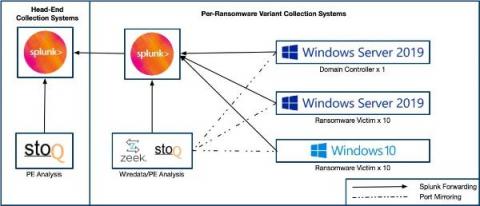
Gone in 52 Seconds...and 42 Minutes: A Comparative Analysis of Ransomware Encryption Speed
Do you feel like every other cybersecurity news story mentioned ransomware in 2021? Does it feel like you can’t turn on a cybersecurity podcast and not hear the “R” word? We feel the same way, and as a cybersecurity vendor, we felt that we should also contribute to the noise. :-) But we did want to try and do something different.
Choosing the Right Metadata Store: Part 1
Rubrik CDM is scale-out and fault-tolerant. Our software runs as a clustered system consisting of multiple nodes, where each node runs an identical copy of our software stack; each node is equally able to perform operations like data protection and recovery. To increase capacity a user simply adds more nodes. The system continues to operate when a node fails, other nodes pick up the workload while the node is offline. Scale-out, fault-tolerant products are built on distributed systems.
Analyzing Exmatter: A Ransomware Data Exfiltration Tool
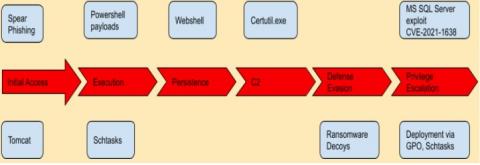
Having conducted more than 3,200 incident response engagements in 2021, Kroll’s Threat Intelligence team now tracks more than 200 ransomware threat actor groups. Kroll’s global Incident Response teams are very familiar with actions traditionally associated with a network intrusion, from initial access to lateral movement to privilege escalation to data exfiltration—and in the case of financially motivated actors, ransomware deployment.
Office Documents and Cloud Apps: Perfect for Malware Delivery
Microsoft Word, Excel, PowerPoint, and other Office document formats are popular among attackers, who abuse them to infect their victims with ransomware, infostealers, backdoors, and other malware. In this article, we look at the anatomy of a recent Office document attack from the victim’s perspective, highlight the most common types of Office document attacks seen today, and suggest strategies to reduce your risk of becoming the latest victim.
Frequently Asked Questions about Rubrik Cloud Vault
At the Rubrik Data Security Spotlight, we introduced Rubrik Cloud Vault, our fully managed, secure, and isolated cloud vault service built on Microsoft Azure. Rubrik Cloud Vault enables customers to build a comprehensive and multi-layered data protection strategy to be cyber resilient.
Ransomware Attacks: How to Mitigate Risk and Protect Your Data
Protestware is trending in open source: 4 different types and their impact
A few days ago, Snyk reported on a new type of threat vector in the open source community: protestware. The advisory was about a transitive vulnerability — peacenotwar — in node-ipc that impacted the supply chain of a great deal of developers. Snyk uses various intel threat feeds and algorithms to monitor chatter on potential threats to open source, and we believe this may just be the tip of a protestware iceberg.
Conti Ransomware: An Analysis of Key Findings
As tax deadlines approach, Emotet malware disguises itself in an IRS email
With just a few weeks until the April 15 deadline for US individuals and businesses to file their tax returns, scammers are as busy as ever. Security researchers at Cofsense have warned that they have seen a number of malicious email campaigns which pose as communications from the Internal Revenue Service (IRS). The emails which purport to come from “IRS.gov”, claim to contain tax forms (such as a W-9) that need to be filled out by the recipient.
Tackling NCSC Guidance - Part 2 (Data Security)
In part one of this two-part blog series, we analyzed the UK National Cyber Security Centre’s (NCSC) guidance relating to backups and data protection. Now in this post, we will examine NCSC’s guidance around mitigating malware and ransomware attacks. Recall that NCSC, at present, provides information and practical guidance in various articles on its website rather than formal requirements or regulations.
Falcon OverWatch Threat Hunting Uncovers Ongoing NIGHT SPIDER Zloader Campaign
Over recent months, the CrowdStrike Falcon OverWatch™ team has tracked an ongoing, widespread intrusion campaign leveraging bundled.msi installers to trick victims into downloading malicious payloads alongside legitimate software. These payloads and scripts were used to perform reconnaissance and ultimately download and execute NIGHT SPIDER’s Zloader trojan, as detailed in CrowdStrike Falcon X™ Premium reporting.
Detecting HermeticWiper
As stated in our previous threat advisory STRT-TA02 in regards to destructive software, past historical data suggests that for malicious actors to succeed in long-standing campaigns they must improve and add new ways of making their payloads stealthier, resistant, and damaging. HermeticWiper introduces some unique features, applying destructive actions on compromised hosts.
Ragnar Locker ransomware - what you need to know
Ragnar Locker is a family of ransomware, which first came to prominence in early 2020 when it became notorious for hitting large organisations, attempting to extort large amounts of cryptocurrency from its victims.
To Be CONTInued? Conti Ransomware Heavy Leaks
Russian-linked malware cyberattacks: what you need to know about Hermetic Wiper and Cyclops Blink
Just days after Russia launched its invasion against the people of Ukraine, news reports emerged of several cyberattacks. Deployed systematically ahead of the land invasion, Russian cyberattacks against Ukraine have rendered Ukrainian banks, government departments and other core services unavailable through the use of sophisticated ‘data wipers
2021 Prediction: Mobile will enable ransomware
What is Malware & How to Protect Ourselves From Computer Viruses
Do you remember when viruses used to be funny and not such a big deal? Maybe a cat would constantly pop up on your desktop or you’d get spammed with hundreds of ads for male enhancement pills? Well, the early 2000s are over (yes, it’s depressing) and malware has advanced far beyond its somewhat quirky origins. Today, viruses have become extremely sophisticated and it’s difficult to know for sure if your files have been infected or not. So what is malware exactly?
PHOREAL malware targets the Southeast Asian financial sector
Elastic Security discovered PHOREAL malware, which is targeting Southeast Asia financial organizations, particularly those in the Vietnamese financial sector. Given the continuous pace of malware development, it's no surprise that adversarial groups will leverage successful campaigns as the basis of developing future attacks, and the recently discovered backdoor campaign targeting Vietnamese financial services is no exception.
Introducing Zero Trust Data Security
Are you ready for Windows 11?
Windows 11 is coming. Ever since its release in October 2021, users have been checking for updates, eagerly waiting to upgrade. Microsoft’s requirements are stricter than usual, and thus the feature rollout is coming in episodes. Existing Windows 10 users can download it for free. For the rest, there are a few compatibility checks before upgrading.
Monitoring Cyber Threats Tied to the Russia-Ukraine Conflict
Beyond the disturbing images of the invasion of Ukraine that began February 24 are the invisible cyberattacks that preceded it and continue to be waged on Ukraine by Russian state-sponsored and other threat actors, which also threaten the West. Vedere Labs, Forescout’s threat intelligence and research team, is closely monitoring the evolution of cyber activities connected to the Russian-Ukrainian conflict.
How to Mitigate the Risk of Ransomware Attacks
US legislation brings mandatory cyberattack and ransomware reporting one step closer
The US Senate has passed legislation designed to improve the cybersecurity of the Federal Government. The legislation, which consists of three bills, was unanimously passed by the Senate on Tuesday evening, and would – amongst other things – require organisations working in critical industry sectors to alert the US Government about hacks and ransomware attacks.
Threat intelligence is your first line of ransomware defense
Plymouth, Inc Recovers in 48 Hours and Zero Data Lost From Security Breach
Decryptable PartyTicket Ransomware Reportedly Targeting Ukrainian Entities
On Feb. 23, 2022, destructive attacks were conducted against Ukrainian entities. Industry reporting has claimed the Go-based ransomware dubbed PartyTicket (or HermeticRansom) was identified at several organizations affected by the attack,1 among other families including a sophisticated wiper CrowdStrike Intelligence tracks as DriveSlayer (HermeticWiper).