Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
4 Things to Know about Your Car and API Security
It used to be cool if your car had GPS and a dashboard screen, remote lock on a key, and a video player for the kids to watch movies during road trips. Then came bluetooth for your phone and keyless start. Not anymore. The bells and whistles available in today’s cars have left them all in the dust. Video player? Let’s be honest. This generation knows and expects on-demand streaming to keep them entertained. Cars can now function as fully equipped communications centers.
8 Most Common Cloud Misconfigurations to Look Out For
Recently, Amazon accidentally exposed information on Amazon Prime Video viewing habits to the public. In addition, Thomson Reuters news and media company admitted that their servers had compromised 3TB of data by public-facing ElasticSearch databases. Well, these are the type of news we often see on the front page of cybersecurity forums. But if you dig a bit deeper, you will find that these data leaks are caused by misconfiguration, not cyber attacks.
6 App Security Tips to Keep Your Application Secure
App security is essential to help deliver the best user experience possible. Read on for more information on keeping your application secure.
The Impact of AI on Cybersecurity: Balancing the Risks and Opportunities
As artificial intelligence (AI) advances, I am seeing a lot of discussion on LinkedIn and in the online media about the advantages it may bring for either the threat actors (“batten down the hatches, we are all doomed”) or the security defence teams (“it’s OK, relax, AI has you covered”).
Does Your Organization Meet the 9 Core Capabilities Essential for Zero Trust in IoT?
Every one of your IoT devices has their own machine identity. But how are these identities the key to achieving Zero Trust IoT project? Today’s PKI (Public Key Infrastructure) vendors have specific solutions for managing non-human identities – machines – like servers, laptops, software applications, API’s and other assets found within a corporate network.
Any2Cloud to Recover Kubernetes Clusters from GKE to AKS
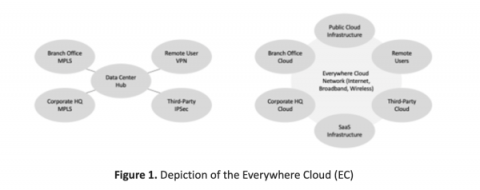
Corelight for the everywhere cloud
Editor's note: This is the first in five-part series authored by Ed Amoroso, founder and CEO of TAG Cyber, which will focuses on how the Corelight platform reduces network security risks to the so-called Everywhere Cloud (EC). Such security protection addresses threats to devices and assets on any type of network, including both perimeter and zero-trust based.
Identity Verification APIs Explained: Identity Verification Services in India
Over the last 3 years, Identity Verification in India has seen a marginal boost in the number of verifications conducted digitally. The market growth in the identity verification sector comes as an effect of the disastrous pandemic that caused record-high identity theft, ATOs, and numerous other frauds all initiated through fake identities, resulting in rapid innovation in identity verification API.
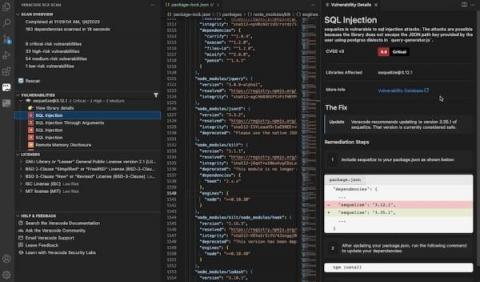
6 Reasons You Need to Run SCA Scans on Projects in VS Code
We love open-source software (OSS). Not only does it save time and effort, but it’s also incredibly rewarding to collaborate with other developers on major projects. Plus, it opens the door for innovation that otherwise wouldn’t be possible at this scale. However, with code comes responsibility, and so it’s imperative to understand the risk OSS libraries carry when we’re integrating them into projects.