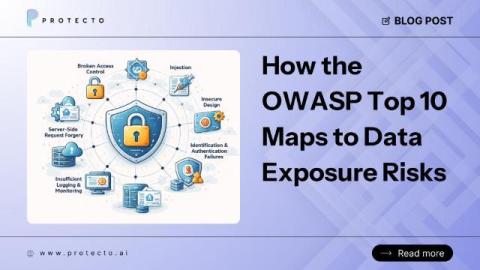
How OWASP Top 10 Maps to Data Exposure Risks: 5 Hidden Threats Explained
Most teams learn the OWASP Top 10 as a list of application security failures. Injection flaws. Broken access control. Security misconfiguration. Items to scan for, remediate, and close before the next audit or penetration test. But data exposure rarely arrives neatly packaged as a single OWASP finding. When sensitive data leaks, it is almost never because one category failed in isolation.