Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
EMC File Activity Monitoring
In this blogpost, we will take a close look at file access auditing on an EMC Isilon file system by leveraging native technologies. We will walk through the configuration process and explore the common challenges faced when working with the resultant audit logs.
Sick of that Security Questionnaire? Automation is the Answer
Security questionnaires (SQs) are not fun. They’re time-consuming, tedious work and sometimes, they’re the one thing standing between you and a closed deal. Fortunately, the emergence of AI in the security space has resulted in many day-to-day workflows being streamlined – with SQs being one of them. Security questionnaire automation solutions have been on the rise.
Devo Exchange - Windows Systems Audit Activeboard
The Consequences of Weakening Patent Rights
National Australia Bank executes world-first cross-border stablecoin transaction, powered by Fireblocks
National Australia Bank has completed an intra-bank, cross-border transaction using NAB-issued stablecoins. This represents a world-first by a major financial institution on a layer-one public blockchain (Ethereum). The pilot transaction involved the deployment of stablecoin smart contracts for 7 major global currencies, namely Australian, New Zealand, Singapore and US dollars, Euro, Yen, and Pound Sterling.
Testing and Assessment for High Assurance
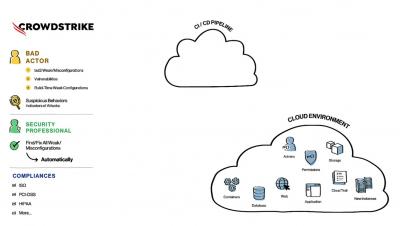
Cloud-Native Application Security Explained
ARMO adds CIS EKS benchmark
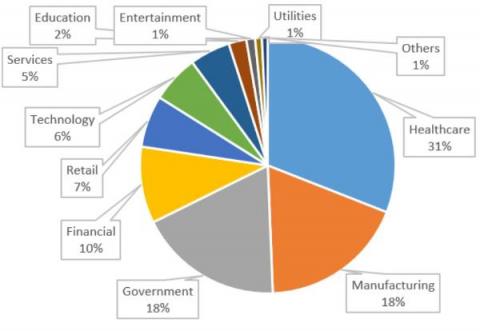
VMware ESXi Servers: A Major Attack Vector for Ransomware
In our new threat briefing report, Forescout’s Vedere Labs provides details on the recent ransomware campaign targeting VMware ESXi virtualization servers, or hypervisors, and analyzes two payloads used in these attacks: variants of the Royal and Clop ransomware. We also present the tactics, techniques and procedures (TTPs) used by attackers in this campaign, discuss mitigation recommendations and list indicators of compromise (IOCs) that can be used for detection or threat hunting.