Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Understanding the new Interpreter flag
How resilient is your supply chain?
This week kicks off the 6th annual National Supply Chain Integrity Month, an initiative started by CISA and other government agencies to highlight the importance of securing our nation’s most critical systems. This year’s theme, “Supply Chain Risk Management (SCRM) – The Recipe for Resilience,” is meant to encourage all stakeholders to apply a comprehensive approach in their efforts to strengthen cyber defenses.
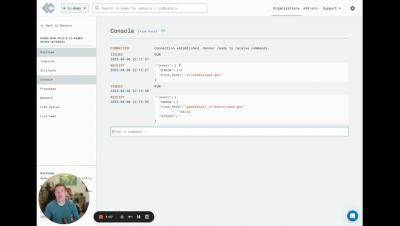
Introduction to Teleport
Recently Exposed North Korean Threat Actor APT43 Targeting Organizations With Spear Phishing
Google’s Threat Analysis Group (TAG) has published a report describing the activities of “ARCHIPELAGO,” a subset of the North Korean state-sponsored threat actor APT43. ARCHIPELAGO’s operators frequently impersonate real journalists or experts in order to make initial contact with their targets.
New Emotet Phishing Campaign Pretends to be the IRS Delivering W-9 Forms
A newly documented phishing campaign demonstrates how timely themes can be impactful in creating a successful attack that gets the recipient to engage with malicious content. As we approach this year’s deadline for filing taxes in the U.S. for 2022, security researchers from Malwarebytes have provided details of an IRS-themed phishing email received by their very own Senior Director of Threat Intelligence.
FBI: Business Email Compromise Attacks Are Being Used to Make Bulk Goods Purchases from Vendors
A new public service announcement focuses on a specific form of BEC attack using little more than a spoofed domain and common vendor payment practices to steal hardware, supplies and more. When I talk about BEC attacks, it’s usually a digital fraud type of attack where legitimate funds being paid to a vendor are diverted to an attacker-controlled bank account by means of the attacker using a spoofed domain or via email compromise.
The Dark Web Cautionary Tale: Infiltrating Criminal Gangs
CI Fuzz - Monthly Coffee Hour
The Next Generation of Risk Registers is Here
A risk register is a tool used to manage potential problems or risks within an organization. It helps to identify and prioritize risks, their likelihood of occurrence, and provides ways to mitigate them. Risk registers allow you to play offense and defense – you’re proactively planning for potential challenges and minimizing their impact on your project’s success in the event that the roadmap does veer off course.