Microsegmentation That Stops Lateral LAN Threat Movement with the Cato LAN NGFW
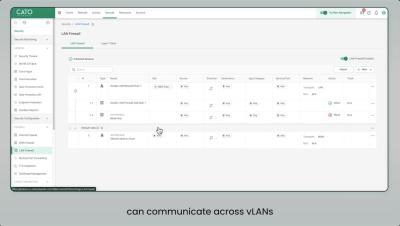
Stop Lateral Threat Movement with Cato’s LAN Next-Gen Firewall! Traditional VLAN-based segmentation is no longer enough to stop lateral movement within your corporate network. Attackers exploit east-west traffic, moving undetected between users, devices, and workloads. How do you enforce microsegmentation without increasing operational complexity? Cato Networks introduces L7 LAN NGFW, a native feature of the Cato SASE Cloud Platform that brings application-aware security to your local LAN. It prevents unauthorized access and restricts communication across VLANs without manual configurations or complex ACLs.