Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
How much does an ISO 27001 certification cost? A full breakdown for 2025
Businesses looking for serious compliance street cred often turn first to ISO 27001. ISO 27001 is a globally recognized framework that outlines and defines information security management system (ISMS) requirements. Because being ISO 27001 certified demonstrates an organization meets best practices for information security, ISO certification can give businesses a significant competitive advantage. If you’re weighing ISO 27001 vs.
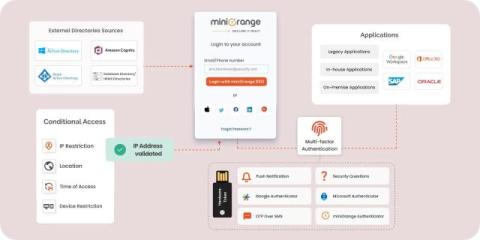
9 Essential Features for Identity and Access Management (IAM) Solution
As businesses rely more on digital ecosystems, securing identities and managing access is important. This blog highlights the top IAM features that protect digital assets while optimizing efficiency.
The 7 Most Telling Data Breaches of 2024
While cyber criminals continue to devise ever more creative ways to get into systems, the outcomes of repeat like a broken record: stolen data and lost money. It happened in again and again this year, but our pick proves the stakes are only getting higher with time. We'll explain the logic behind the list, impacts felt, and key takeaways.
Emerging Threat: Palo Alto PAN-OS CVE-2024-3393
CVE-2024-3393 is a high severity (CVSS v4.0 score 8.7) Denial of Service (DoS) vulnerability affecting specific versions of Palo Alto Networks PAN-OS DNS Security feature. This vulnerability allows unauthenticated attackers to send malicious packets through the data plane of the firewall. This forces the firewall to reboot. Repeated attempts can force the firewall into maintenance mode, requiring security teams to manually reset the firewall and significantly disrupting operations.
IT Resource Management: Why It Is A Key To Business Success
To achieve success with your project, you should pay close attention to how you manage your IT resources. If these are allocated correctly, it is easier to stay within budget, maximize the productivity of your employees or teams, and, most importantly, – deliver a high-quality project on time. However, managing these resources effectively takes time and a lot of effort.
Cybersecurity as a Service: Reliable Protection for Businesses
Cyber risks are changing at a speed that has never been seen before. Hackers are always looking for vulnerable spots in businesses, no matter how big or small they are. Cybersecurity as a service has become a game-changing option that gives businesses strong, scalable, and affordable security. Businesses can protect their networks, data, and processes with this model, which is provided by experts, without having to build a large security team in-house.
Why Your Business Needs MDR Security for Proactive Threat Protection
It's more important than ever to stay ahead of possible risks in today's fast changing cyber threat landscape. You can't just use old-fashioned security steps to keep your business safe from modern attacks. This is where Managed Detection and Response (MDR) security comes in and changes everything.
Audit Log Management: Essential Practices and Key Comparisons
Audit logs are important in maintaining the security of an organization's information systems. They record all the events taking place in a system, including log-on attempts, file access, network connections, and other important operations. Therefore, these logs must be monitored and analyzed effectively. This is achieved through audit log management.
What To Know About the FBI's Warning Encouraging Encrypted Messaging
The Federal Bureau of Investigation (FBI) recently issued a warning that iPhone and Android users should begin using encrypted messaging apps to protect the privacy of their communications from foreign hackers. The FBI issued this warning after Salt Typhoon – a Chinese hacking group – infiltrated American networks and began collecting data from phone calls and text messages.