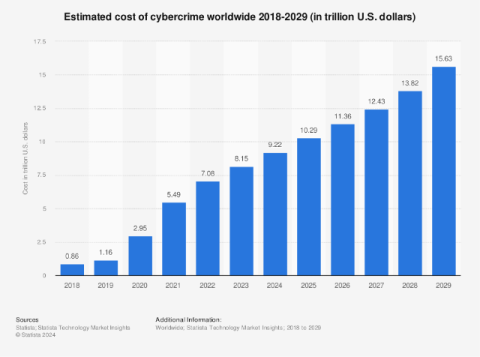
AI in cybersecurity 101: The economics of bot vs bot battles
If you run an online image search for “cyber hacker,” you’ll likely find countless pictures of shadowy, hooded figures hunched over a laptop. There’s just one problem with those search But here’s the catch: The image of a human hacker is in the minority these days.