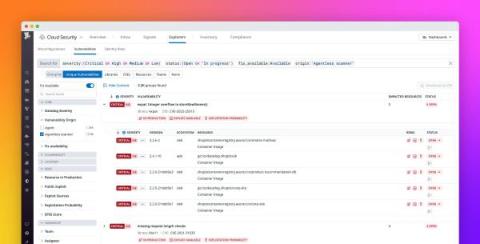
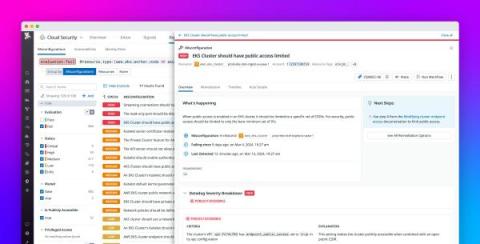
Detect vulnerabilities in minutes with Agentless Scanning for Cloud Security Management
Security teams require complete visibility into their hosts, containers, and functions in order to detect, prioritize, and remediate their most pressing security risks. The Datadog Agent helps you achieve this visibility by collecting deep insights in your environment through logs, distributed traces, infrastructure metrics, and other key telemetry.