Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
This Month in Datadog: State of DevSecOps report, Event Management, Container Image Trends, and more
DevSecOps lifecycle coverage with new Snyk and Dynatrace app
Balancing the volume of applications and the increased deployment frequency with the need for security is a struggle for both development and security teams. Recent research indicates that vulnerability management in modern software development has become more complex, with 69% of CISOs acknowledging this challenge. Consequently, many applications are not adequately covered by security scans.
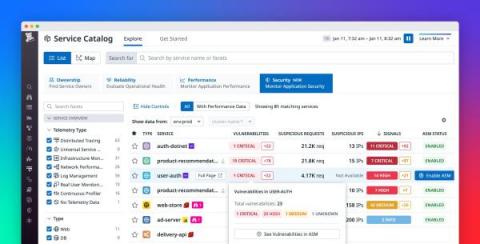
Gain visibility into risks, vulnerabilities, and attacks with APM Security View
As your business grows and your services scale in number and complexity, it’s difficult to maintain a rapid pace of innovation while keeping your applications secure. It’s particularly challenging to respond to attacks, as DevOps and security teams need to collaborate to understand each attack’s root cause and remediate the vulnerabilities that enabled it.
Secure your application development with AWS and Mend
Snyk + Dynatrace workshop: Integrating for real-time vulnerability detection
Since 2019, Snyk and Dynatrace have partnered with a shared mission of securing the entire software development lifecycle (SDLC) and accelerating digital transformation. As many agile organizations migrate their workloads to the cloud, it’s tempting for teams to let security take a back-seat until all the pieces of the infrastructure puzzle are in place.