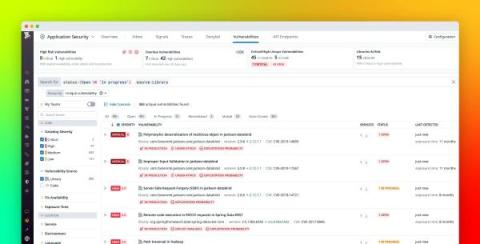
Mitigate vulnerabilities from third-party libraries with Datadog Software Composition Analysis
Mitigating application vulnerabilities throughout the software development life cycle (SDLC) is critical—and challenging, especially as applications rely more and more on third-party, open source software (OSS). With this type of architecture, teams often don’t know exactly where vulnerabilities exist in their code, which of those vulnerabilities are actively exposed in production services, and which vulnerabilities are more critical to address than others.