Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Sensitive Data: What is it, and why you should never share it.
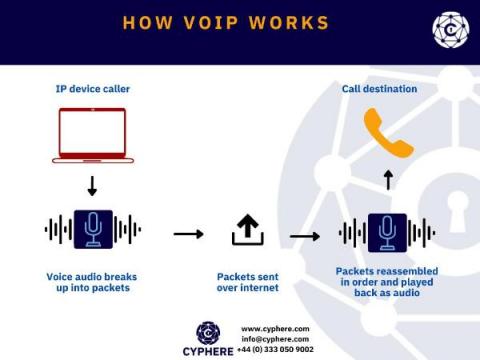
VoIP Security. How secure is your VoIP?
For over a century we have seen voice communication being made over Public Switched Telephone Network (PSTN), but since the past decade or two Voice over IP (VoIP) has been introduced and quickly adopted throughout the world for making business phone calls.
Cybersecurity Architecture: A Complete Guide to Preparing Your Organization for a Cyberattack
Top Cybersecurity Metrics (KPI) to Track
Cyber security KPI or other Key Performance Indicators are established in different areas of every organisation to track and monitor the progress towards attaining a certain goal or target. Cybersecurity is no exception here, and companies should maintain proper cybersecurity KPIs. There are many blog posts available around this topic but in this article, we have gathered a list of important cybersecurity KPIs that every organisation should consider.
Threat hunting: Process, Methodologies, Tools and Tips
In cyber security, threat hunting is the act of proactively searching and monitoring networks, systems, endpoints, datasets etc. to identify any malicious behaviours or patterns that are not detected by existing security tools.
PHP Security 101 + 1
PHP is by far the most widely used server-side programming language. Security threats surrounding PHP applications have been in the news because PHP captures over 80% of the internet with over 10 million websites built. It’s no wonder that with such a massive usage, PHP is also one of the most targeted and exploited languages, as shown in the below statistics.
Information Security Controls | Different Types and Purpose Explained
Security risks of Cloud Computing | Threats, Issues and Challenges
CVE-2021-44228 - Log4j zero day vulnerability, detection and Log4shell fix
Log4j zero-day vulnerability is flooding the security updates/news everywhere. This issue has been named Log4shell and assigned CVE-2021-44228 (still awaiting analysis at the time of writing).