Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Understanding Broken Authentication and Session Management
Benefits of Cyber Security: Importance for Businesses and Individuals
Cyber security is a crucial element of the digital age. You may not notice it, but cyber attacks are happening every day to companies and individuals alike. We’ve got you covered with this detailed guide on the importance and benefits of cyber security along with the mitigation strategies and tips for protection against cyber attacks.
Port 443: What it is & Why we use it
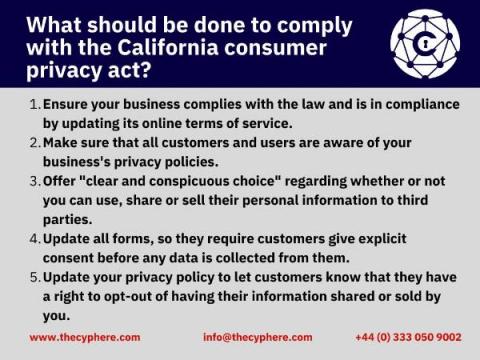
California Consumer Privacy Act (CCPA) Compliance: What you need to know to be compliant
The California consumer privacy act (CCPA) is a law that was passed in 2018, and it is in effect from January 1st 2020. The California attorney general’s office has not taken any enforcement action against firms that did not meet the standards until July 1st 2020. A lot of people are unsure about what this new law means for them. Like the GDPR, there are significant penalties for non-CCPA compliance and potential loss of consumer loyalty.
What Is Penetration Testing? Benefits And Pen Testing Vulnerabilities
What is PCI penetration testing? Requirements and Benefits
Web Application Penetration Testing: Introduction And Benefits
SAAS Security Testing: why it is important and how to do it
Real-life Examples of Phishing Emails
Phishing emails are a serious problem for both businesses and consumers. Phishers use phishing emails to steal users’ personal information, like usernames, passwords, credit card numbers, social security numbers and other sensitive data.