What is Domain Hijacking? Tips to Protect Yourself
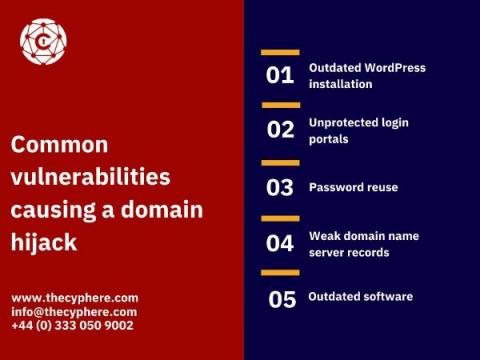
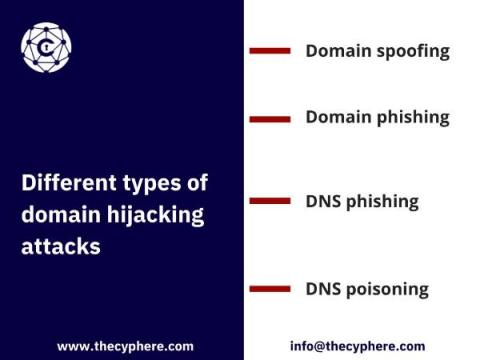
Domain hijacking is the act of domain name theft. It can happen to individuals or organisations and it’s increasing in frequency. The name may be hijacked by someone else who passes themselves off as you, tricks your domain registrar into transferring your domain to them, or hacks into your account (sometimes through phishing) and transfers it themselves.