Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
%term
USA Today Side Steps Targeted DDoS Attack with Sumo Logic
“We’re under attack” may be the three least favorite words of every cybersecurity professional out there. Luckily, for USA Today, this doesn’t happen often, however, last year one of our 115 media markets was targeted by a distributed denial of service (DDoS) attack.
What is Machine Learning?
Over the last century, our technology devices have gone from being clunky systems that require tons of human interaction, to modern machines that seem to have a mind of their own. Our phones can do things like autocomplete sentences before we finish typing, suggest purchases based on sites we’ve visited in the past, and even predict our schedules on any given day based on our prior habits. This is all possible due to the growth of artificial intelligence and machine learning.
Economy of hacking: how do hackers make money?
80% of all human endeavour is committed to making money, with the remaining 20% spent finding interesting ways to spend it. These are figures that I’ve just made up, but I said it in the Bulletproof office, and everyone nodded, which either means it speaks a certain truth or, once again, everyone is doing their best to ignore me. With this in mind, it’s fair to say people tend not to put a lot of effort into something unless they know they’re going to be financially rewarded for it.
Weekly Cyber Security News 01/03/2019
A selection of this week’s more interesting vulnerability disclosures and cyber security news. Lots of buzz around a particularly embarrassing and damaging leak announced yesterday.
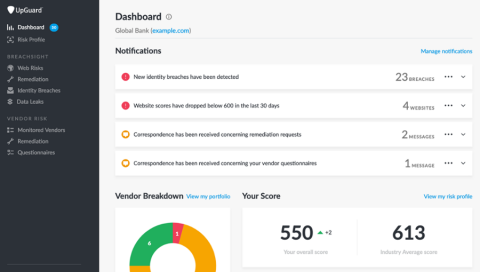
UpGuard's new navigation: CyberRisk is evolving
UpGuard CyberRisk enables organizations to control and monitor third-party vendor risk in real-time and improve their security posture. Since we launched CyberRisk, our team has been speaking to users and evolved the platform into two new modules, BreachSight and VendorRisk. Combined with a redesigned user experience, UpGuard is easier to use than ever.
Top 6 Container Security Lessons from Deploying Kubernetes and Red Hat OpenShift
We recently had the opportunity to share the lessons we have learned about container security from deploying Kubernetes and OpenShift in the field. If you don’t have time to watch the full recording of our conversation, here are a few highlights.
SSAE 18 Updates & Requirements
What Could Losing One Terabyte of Data Cost Your Business?
It’s no secret that your digital footprint is growing. Whether your business has 10 employees in one office or 2,000 employees in offices all over the world, you’re creating more content today than you did two years ago—or 2 months ago for that matter. Along with increased volume, content itself has evolved to encompass much richer media, like HD videos and CAD files.
Understanding the Types of Risk in the Oil & Gas Industry
Defined as critical infrastructure, the oil & gas industry increasingly faces cybersecurity risks as nation-state cybercriminals attempt to undermine other countries. The integration of information technology (IT) systems into operational technologies (OT) creates a unique threat to the oil and gas industry that places both the companies and the public at risk.