Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Active Directory Audit Rules
Hidden Value In Creating Cybersecurity Audit Programs
One of my first tasks after leaving NSA for private industry in the early 90s was to write my new company’s information security policy. I’m not sure my previous job as a cryptanalyst left me qualified for this, but I was viewed as the security guy. So, I attacked the task with vim and vigor. That first information security policy I wrote was a thing of beauty. I scoured the Orange Book and other resources to find every security requirement that might help us prevent a security incident.
CMMC Audit: What is it and how to prepare for it
Business owners whose revenue streams depend significantly or partially on government contracts have been recently faced with the mandatory emerging regulations called Cybersecurity Maturity Model Certification, also known as CMMC. All organizations working with the Department of Defense (DoD) and Federal government as their prime or subcontractors must be audited against these requirements by a competent third-party CMMC auditor.
Turning InfoSec Success into Audit Wins | Tips & Tricks Ep.1
Active Directory Auditing Guidelines
Active Directory and AD Group Policy are foundational elements of any Microsoft Windows environment because of the critical role they play in account management, authentication, authorization, access management and operations. Accordingly, proper Active Directory auditing is essential for both cybersecurity and regulatory compliance.
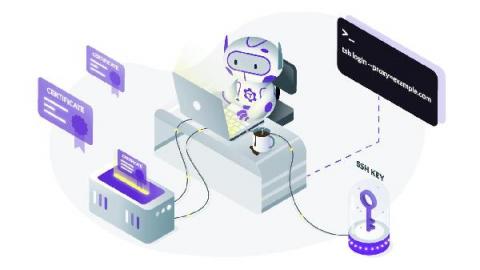
Teleport in 2021: Security Audit Results
We now live in an era where the security of all layers of the software stack is immensely important, and simply open-sourcing a code base is not enough to ensure that security vulnerabilities surface and are addressed. At Teleport, we see it as a necessity to engage a third party that specializes in acting as an adversary, and provide an independent analysis of our sources.
Detect suspicious activity in GCP using audit logs
GCP audit logs are a powerful tool that track everything happening in your cloud infrastructure. By analyzing them, you can detect and react to threats. Modern cloud applications are not just virtual machines, containers, binaries, and data. When you migrated to the cloud, you accelerated the development of your apps and increased operational efficiency. But you also started using new assets in the cloud that need securing.
Collect and monitor Microsoft 365 audit logs with Datadog
Microsoft 365 is a suite of cloud-based productivity and communication services that includes Microsoft Office applications (including OneNote and OneDrive) as well as other popular Microsoft tools like Skype and Teams. Microsoft 365 tools and services are at the core of many organizations’ data management and day-to-day workflows, so monitoring activity across your environment is key to making sure that these services remain secure and meet compliance standards.
FERC Releases Staff Report on Lessons Learned from CIP Audits
In October, the Federal Energy Regulatory Commission (FERC) released its “2020 Staff Report Lessons Learned from Commission-Led CIP Reliability Audits.” The report summarizes the Commission’s observations from Critical Infrastructure Protection (CIP) audits performed in conjunction with staff from Regional Entities and the North American Electric Reliability Corporation (NERC).