Gearing Towards Your Next Audit - Understanding the Difference Between Best Practice Frameworks and Regulatory Compliance Standards
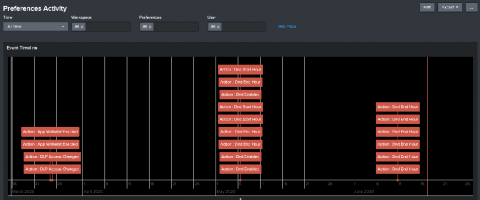
Security configuration management (SCM) can help organizations do much more than just harden their attack surfaces against intrusions. This fundamental control also has the ability to make your audits flow more smoothly. Indeed, it allows organizations to pull reports from any point in time and demonstrate how their configuration changes and alignments help to support their compliance efforts.