The CISO's Checklist: How to Evaluate an API Security Platform
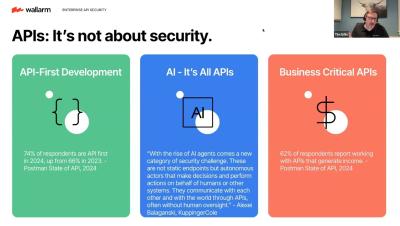
API Security Evaluation Checklist In the first half of 2025, APIs have emerged as the primary focus for attackers. Unlike traditional broad attacks on websites, threat actors are increasingly exploiting vulnerabilities and launching DDoS attacks on APIs, which are often harder to secure and manage at scale. Key insights from the State of Application Security Report H1 2025.