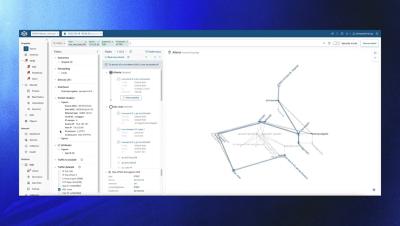
Introducing the New Security-Focused Path Search View in Forward Enterprise
Chris Naish from Forward Networks introduces a new security-centric feature in the Forward Enterprise release version 25.10. The Security Focused Path Search View highlights devices responsible for traffic restriction or IP address translation, improving network path comprehension for security analysis. This mode filters out non-restrictive hops, allowing security professionals to efficiently access crucial information.