Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Tackling your network security challenges using ManageEngine ITOM solutions
Network security management typically entails end-to-end management of the entire network security infrastructure of an enterprise. However, in this rapidly changing security ecosystem, there’s an inherent need for IT admins to be extremely agile to maintain an effective security posture.
What is Security Information and Event Management (SIEM), and how is it evolving?
Halloween is tomorrow, and do you know what that means? For starters, it means you can dance under the rare blue moon. A full moon visible for all time zones on Earth hasn’t happened since 1944, and won’t happen again until 2039. It also means you can don a costume and be anything you like. Kind of like a fraudster, that assumes a new persona every time there is a payment fraud attack.
Devo Service Operations Product Introduction
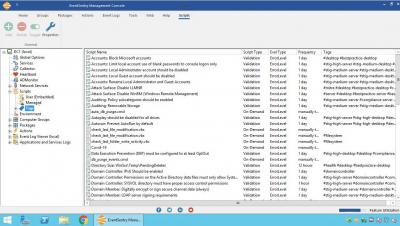
EventSentry v4.2 New Features: Management Console Walk-Through
Sophisticated phishing
Most of us can think of a time when we received a phishing email. In fact, most phishing emails are easy to identify, and automatically go to spam. However, in this ongoing pandemic, hackers are adopting advanced tactics that cleverly conceal their malicious intentions, and fly under the radar by leveraging the victim’s fear, anxiety, or plain negligence.
Track open source security exposure with Snyk and Datadog
Using open source code makes it easier to build applications, but the freely available nature of open source code introduces the risk of pulling potential security vulnerabilities into your environment. Knowing whether or not customers are actually accessing the vulnerable parts of your application is key to triaging security threats without spending hours fixing an issue that doesn’t affect end users.
Enhancing Observability in DevSecOps
How Long Should You Hang Onto Your Data?
One of the most common questions that businesses operating under GDPR, LGPD or other similar data regulations have is how long should you keep data? As answers to this question typically seem to vary widely to clear up confusion, we’ve gathered insights from business leaders & specialists across a variety of industries to try and answer this question and shed light on what are reasonable timeframes to keep hold of data, whether that may be financial, employee or other potentially sensitive data.
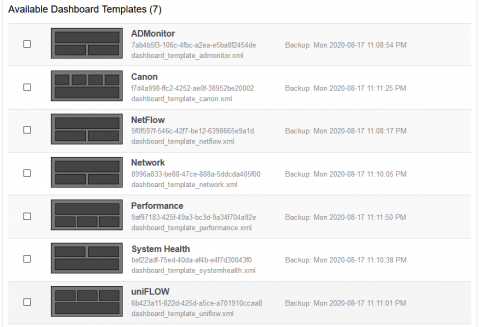
Validating your IT environment, discovering browser extensions & more with EventSentry v4.2
This latest update to EventSentry improves your security posture with validation scripts, simplifies IT troubleshooting for both administrators and users, gives you visibility into installed browser extensions along with many other usability improvements in the web reports.