Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Emerging threats: a view from the front lines
Peace out this holiday season by securing every transaction against card-not-present fraud
We are about to enter the most wonderful time of the year. As consumers increasingly turn towards online and mobile commerce, are you confident in your card-not-present fraud detection capabilities? 2020 has been a year of great surprise and change. While the global health pandemic has changed how we physically interact with each other, it has also revolutionized how we shop.
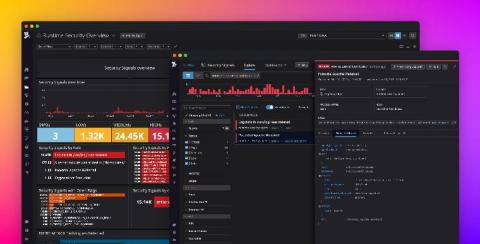
Secure your infrastructure in real time with Datadog Runtime Security
From containerized workloads to microservice architectures, developers are rapidly adopting new technology that allows organizations to scale their products at unprecedented rates. In order to make sense of these complex deployments, many teams are abstracting applications away from the environments in which they run. Because of this trade-off, developers and security teams lose the access to the unified context from infrastructure to application needed to fully secure their services.
7 High-Risk Events to Monitor Under GDPR: Lessons Learned from the ICO's BA Penalty Notice
Hello Security Ninjas, Today's IT world is complex and can be challenging for security operations teams. Nowadays, more apps are being integrated and interconnected than ever before. Cloud services and SaaS solutions purchased all throughout the organization outside of the IT department add even more complexity. Communicating to application and service owners the kind of activities that need to be logged and sent to the SOC can be a daunting task.
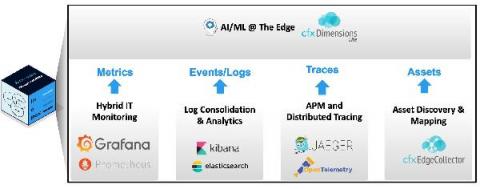
Doing AIOps Right: Addressing Monitoring Gaps with Observability-in-a-Box
3 Benefits of Cyber Security Monitoring Services
Multi-Cluster, Multi-Cloud and Hybrid Cloud Networking, Observability and Security Management
INETCO Recognized as a Leader in Payment Fraud Detection Solutions by Welp Magazine
Fraud is something that occurs every day across a variety of industries, causing trillions in losses each year. Hardest hit are the financial services and banking industries. In a recent article, Welp Magazine shared its top 13 picks for the best fraud detection startups. INETCO was extremely happy to be featured as a part of this list – selected for its innovative product and exceptional growth strategy.
Port scanner 101: What it is and why should you use it
In today’s complex network infrastructure comprised of diverse resources, devices, and users, port scans represent a significant amount of network traffic. Crackers and hackers alike use port scanners to discover port vulnerabilities that can become attack vectors to malicious outcomes. In this post, we discuss the fundamentals of port scanning, and why you need to deploy an effective port scanner software on your network right now.