Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Imperatives for Today's Security Transformation
Industry research firm Gartner asked cybersecurity thought leaders to submit a video of themselves answering the question “What are your customers’ top security priorities?” for the Gartner Security & Risk Management Summit, a virtual event for the EMEA region held this month. Julian Waits, general manager of cybersecurity for Devo, was among those to whom Gartner posed the question. His video is below, and this blog post offers an expanded version of his response.
ELK - Not Just For The Nice Visitors
Most of the applications we see for the ELK stack are from businesses which want to improve their customers' experience. To return relevant search results and to create Kibana dashboards that allow them to analyse data and give the customers what they want. But there are some cases where the customer is always wrong, and where the last thing you want to do is give a site visitor what he wants. Welcome to the world of forensics, compliance and fraud detection.
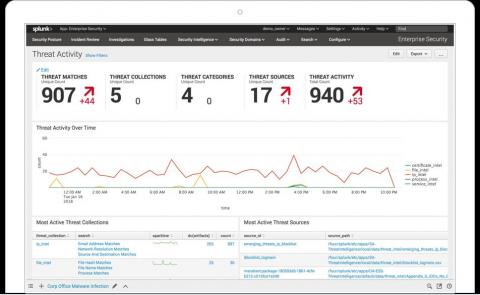
Why Threat Intelligence Sharing is the Future of SOC Analyst Productivity
With all the cyberthreats around today, security operations center (SOC) analysts need the right tools to identify, respond to, and stop those threats. Increasingly, threat intelligence sharing is one of the key tools for preventing threat actors from breaching organizations’ network, infrastructure, and operational environments, including the cloud.
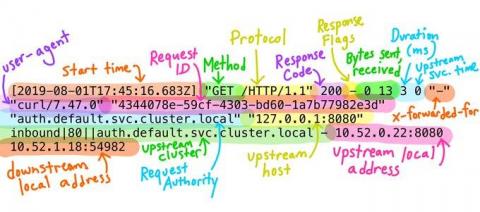
Monitor Alcide kAudit logs with Datadog
Kubernetes audit logs contain detailed information about every request to the Kubernetes API server and are critical to detecting misconfigurations and vulnerabilities in your clusters. But because even a small Kubernetes environment can rapidly generate lots of audit logs, it’s very difficult to manually analyze them.
Don't Let Security Go Up, Up and Away (in the Clouds), Start with Data
Security teams can’t defend what they can’t see. As organizations move more workloads to the cloud, security teams need added visibility into these new workloads or risk having blind spots that lead to compromise. In the first installment of our "Getting Data In" webinar series, "Modernizing your SOC for the Cloud Age Starts with Security Foundations," we demonstrate how to quickly and easily onboard data into Splunk Cloud.
Introducing a New Splunk Add-On for OT Security
The lines Between IT and OT are blurring. With IT and Operational Technology (OT) systems converging, ensuring the security of devices, applications, physical locations and networks has never been more difficult or more important. There is a growing recognition by security professionals that they have a readiness and visibility problem in plain sight.
Elastic Security - Unified Protection for Everyone - Aug 13, 2020 Elastic meetup
Elastic 7.9 released, with free distribution tier of features of Workplace Search and endpoint security
We are pleased to announce the general availability of Elastic 7.9. This release brings a broad set of new capabilities to our Elastic Enterprise Search, Observability, and Security solutions, which are built on the Elastic Stack — Elasticsearch, Kibana, Logstash, and Beats.
Upping the Auditing Game for Correlation Searches Within Enterprise Security - Part 1: The Basics
One question I get asked frequently is “how can I get deeper insight and audit correlation searches running inside my environment?” The first step in understanding our correlation searches, is creating a baseline of what is expected and identify what is currently enabled and running today. Content Management inside Splunk Enterprise Security is a quick way to filter on what is enabled (and it’s built into the UI and works out of the box).