Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Monitoring health information systems with HIPAA-compliant logs
As healthcare and life sciences organizations move to digitize their operations and automate their workflows, they are encountering new challenges related to HIPAA regulations, which dictate how patient information should be collected and stored.
Integrating Attack Behavior Intelligence into Logstash Plugins
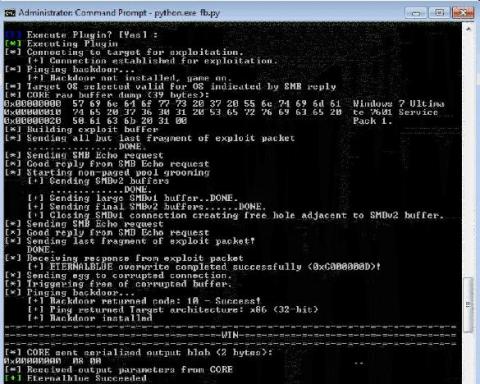
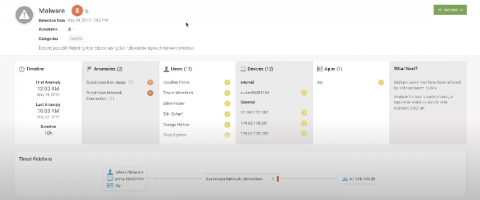
Detecting Malware and Watering Hole Attacks with Splunk UBA
You may be surprised to learn that a particular malware is responsible for data theft in over 20% of financial institutions and other verticals in 2019. Watering hole attacks involve a web server that hosts files or applications where the website or files on the site become weaponized with malware. While recent news cycles have shined a spotlight on ransomware and crimeware, malware is not a new concept.
Protect Your AWS Infrastructure with GuardDuty and Coralogix
Cloud environments like AWS can be a challenge for security monitoring services to operate in since assets tend to dynamically appear and disappear. Making matters more challenging, some asset identifiers that are stable in traditional IT environments like IP addresses are less reliable due to their transient behavior in a cloud service like AWS. Amazon GuardDuty protects your AWS environment with intelligent threat detection and continuous monitoring.
Prevent and Detect Threats Across Multi-Cloud Environments
The cloud has become ubiquitous in all we do, and the line between the perimeter and the cloud continues to shrink as most enterprise organizations are looking to shift their cloud strategy to a multi-cloud approach. Moving to the cloud comes with plenty of benefits like performance optimization, improved reliability and overall cost savings, but cloud adoption is not without its risks and challenges.
Okta Log Insights
This post will show you how Coralogix can provide analytics and insights for your Okta logs, both performance, and security. Okta is one of the leading Identity provider platforms in the world, offering a variety of cloud services including a Single Sign-On solution to manage and secure company user authentication with 3rd party applications.
Continuous Intelligence for Atlassian tools and the DevSecOps Lifecycle (Part 1)
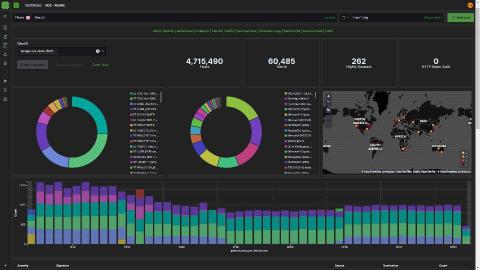
Léargas Security chooses Elastic, drops Splunk to battle COVID-19 fraud
Léargas Security (Léargas is Gaelic for “insight”) provides clients with actionable insights into anomalous or abstract behaviors through the correlation of data gathered from converged security controls: cyber and physical.
A Checklist for Effective Threat Hunting Tools
Threat hunting is one of the most critical activities performed by SOC teams. Once an alert triggers and a tier-1 analyst assesses it and sends it up the line for further evaluation by a more senior analyst, the race is on. Hunting down the threat as quickly as possible, before it can wreak havoc on the organization, becomes the top priority.