Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
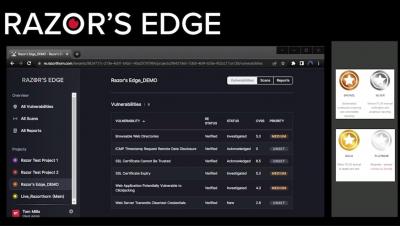
Continuous Penetration Testing: discover the Razor's Edge platform from Razorthorn
Creating Trust in an Insecure World: Strategies for Cybersecurity Leaders in the Age of Increasing Vulnerabilities
Vulnerabilities are on the rise, and it's not just the number that's growing; the severity of these vulnerabilities is also increasing. Cybercriminals are taking advantage of these vulnerabilities to launch sophisticated attacks, leading to data breaches, ransomware, and other devastating cyber incidents.
EP 24 - Making the Leap to Post-Quantum Computing Encryption
Quantum computing is coming and it has the potential to be both exciting and terrifying… On today’s episode of Trust Issues, host David Puner speaks with cryptographer Dr. Erez Waisbard, CyberArk’s Technology and Research Lead, about quantum computing innovation and its cybersecurity implications – from data encryption to surveillance and privacy. Dr.
The Evolution of Qakbot: How Cato Networks Adapts to the Latest Threats
The world of cybersecurity is a never-ending battle, with malicious actors constantly devising new ways to exploit vulnerabilities and infiltrate networks. One such threat, causing headaches for security teams for over a decade, is the Qakbot Trojan, also known as Qbot. Qakbot has been used in malicious campaigns since 2007, and despite many attempts to stamp it out, continues to evolve and adapt in an attempt to evade detection.
Helping protect personal information in the cloud, all across the world
Cloudflare has achieved a new EU Cloud Code of Conduct privacy validation, demonstrating GDPR compliance to strengthen trust in cloud services.
DNS-Based Threats and Their Impact on Business
A Domain Name System (DNS) is a protocol that translates human-readable domain names/URLs—like favoritewebsite.com—into IP addresses that computers can read—like 135.24.56.98. DNS servers handle tens of thousands of queries that transfer minute bits of data between devices, systems, and servers—which makes DNS an attractive and easily exploitable vector for hackers (Cloudns.net).