OpenStack Tutorial: How to One-Click Restore OpenStack Workloads with Trilio
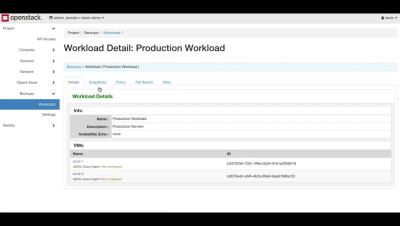
Trilio for OpenStack Tutorial - One Click Restore Trilio is the OpenStack-native data backup and recovery solution that gives OpenStack users the ability to restore entire workloads with one click. Trilio helps OpenStack users protect their clouds and efficiently create, store and manage point-in-time backups while providing policy-based recovery times to meet application SLA’s. Trilio is not a third-party legacy solution. It is the OpenStack-native backup service.