Data driven detection: Corelight's approach to AI-powered NDR
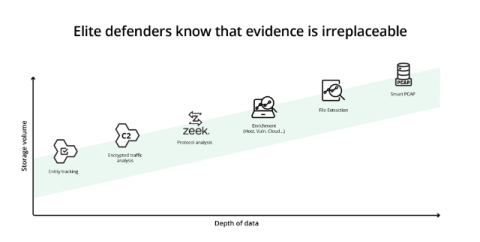
The Gordian knot of any detection strategy is knowing that two conflicting ideas are both true. On one hand, every SOC needs as much accurate detection coverage as they can get to find and disrupt attacks. On the other, the attackers you REALLY care about will find a way to bypass those detections so you need the ground truth of the attacker behavior on your network. The only answer is to have both: the absolute best data and the broadest detection suite possible on top of it.