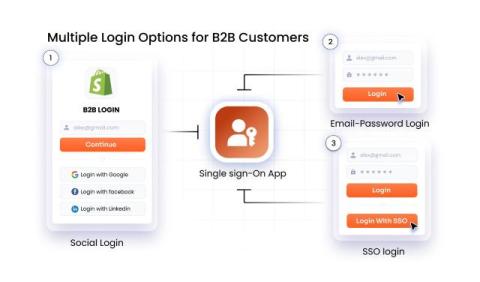
Flexible Login Options for Shopify B2B - SSO, Social Login & More
Struggling with login restrictions on Shopify B2B stores? Learn how to enable custom authentication for Shopify B2B customers and support multiple login methods (Email-Password, Phone-OTP Login, Social Login, Single Sign-On, etc.) for Shopify Customer Accounts with miniOrange solutions.