Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Tanium and Microsoft Are Better Together - That's Why They Named Us Partner of the Year
Tanium and Microsoft allow customers to implement a zero-trust ecosystem, bringing visibility, control, and remediation to security and operations teams.
A Red Team's Perspective: How to Scope a Penetration Test
Penetration testing is a crucial part of a comprehensive cybersecurity plan. By simulating a real-world attack, a penetration test can help identify vulnerabilities and weaknesses across systems, networks, and applications before a malicious actor can exploit them. To get off on the right foot with a penetration test and get an accurate timeline and budget for the test, it’s important to have a proper scope. Learn how to scope a penetration test from the perspective of the Sedara Red Team.
What is the Mitre ATT&CK Framework?
In cybersecurity, being well-versed in the wide range of resources available for protecting and enhancing your digital environment is crucial. One of the most significant and effective tools is the Mitre ATT&CK Framework. Read on for an in-depth exploration of this critical cybersecurity framework and how you can apply it to your own organization.
CIS Critical Security Controls 101: Everything to Know About the 18 Controls
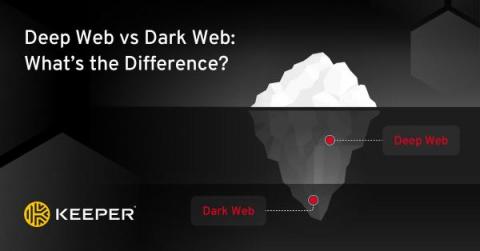
Deep Web vs Dark Web: What's the Difference?
The main difference between the deep web and the dark web is that the deep web is bigger and used every day by most people without even realizing it. The dark web can only be accessed with the Tor browser and is riskier to access than the deep web. Continue reading to learn more about the differences between the deep and dark web, and how you can keep your information protected from both.
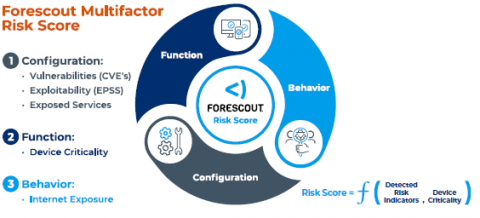
Go Beyond Device Visibility to Prioritize and Act on Cybersecurity Risk
When I joined Forescout as CEO six months ago, I was excited to partner with our strong employees, management team and board as we take the company through its next phase of growth. Today I’m pleased to announce enhancements to the Forescout® Platform that will help customers fully understand the risk posture of their attack surface and enable their security teams to focus on remediating the assets that pose the most risk.
Using insecure npm package manager defaults to steal your macOS keyboard shortcuts
Malicious npm packages and their dangers have been a frequent topic of discussion — whether it’s hundreds of command-and-control Cobalt Strike malware packages, typosquatting, or general malware published to the npm registry (including PyPI and others). To help developers and maintainers defend against these security risks, Snyk published a guide to npm security best practices.
Free CCPA Vendor Questionnaire Template (2023 Edition)
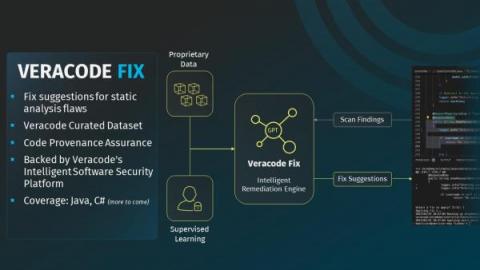
How to Measurably Reduce Software Security Risk with Veracode Fix
Veracode Fix is now available as an add-on to Veracode Static Analysis for customers on the North American instance. Availability for customers on Veracode’s EMEA and FedRAMP instances will be coming soon!