Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
The Cybersecurity Analytics Ultimate Guide
WatchGuard Honored in CRN's 2023 MES Midmarket 100
Today, we are thrilled to share that WatchGuard has again been honored as part of CRN’s MES Midmarket 100 list for 2023! CRN’s prestigious annual MES Midmarket 100 program recognizes forward-thinking vendors that serve midsize customers with products and services designed to address the midmarket's unique needs.
What is The Network and Information Security 2 Directive (NIS2)?
The Network and Information Security 2 (NIS2) Directive is the European Union's (EU) second attempt at an all-encompassing cybersecurity directive. The EU introduced the legislation to update the much-misinterpreted Network and Information Security (NIS) Directive (2016) and improve the cybersecurity of all member states. It signed NIS2 into law in January 2023, expecting all relevant organizations to comply by October 18th, 2024.
How Improved Visibility Helps Achieve Compliance
In the ever-evolving cybersecurity landscape, businesses face an exhaustive battle to safeguard their valuable data while complying with industry regulations. To address these challenges, innovative solutions have emerged to enhance network security. Network visibility remains a crucial focus. The profound impact of heightened visibility cannot be ignored, as it plays a crucial role in fortifying network security and achieving compliance objectives.
Drowning in Data? Endpoint Security "Lifeguard" Strategies Can Help
Just as lifeguards vigilantly safeguard swimmers at the beach, endpoint security plays a critical role in protecting our digital environment.
Changes to NIST CSF 2.0: GRC Newsflash
At TrustCloud, we’re on a mission to democratize compliance, so we’re kicking off GRC Newsflash – a series where our experts give you a quick rundown on the latest buzz happening in the GRC, security, and privacy world. Today’s edition features our Compliance Specialist Frank Kyazze, and covers updates of the NIST Cybersecurity Framework 2.0, announced on August 8, 2023.
Protecting Local Government Data: Why Password Managers Are Essential
Cyberthreats and ransomware attacks can be crippling for municipalities and county government offices. Local government employees need to access a growing number of systems, applications and databases to perform their duties, while the rise of remote work has drastically increased the attack surface of a typical small government office.
INETCO in the News: Commentary: How Emerging Technologies Can Help Solve EBT Fraud
Ali Solehdin – Digitaltransactions.net – August 11, 2023 Instances of electronic benefits transfer (EBT) fraud have become more prevalent in the United States as criminals become more brazen and increasingly prey on society’s most vulnerable.
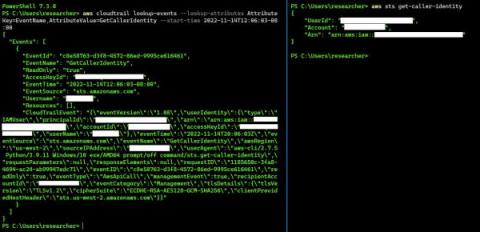
How to Enable Logging: Secure Cloud-native Development Series
Build secure cloud-native applications by avoiding the top five security pitfalls we lay out in our Secure Cloud-native Development Series. This blog is the second part of the series, and it will teach you how and why to enable logging from the start. We’re going to talk about enabling logging (cloud logging, to be specific). What’s the difference? Not much, other than the fact that it’s another managed service integrated with the tools we should already be utilizing.