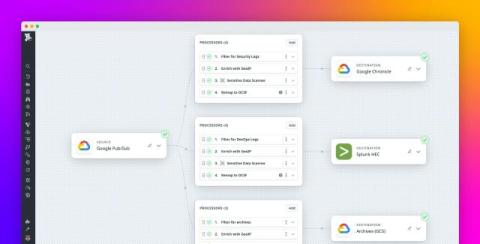
Streamline your security workflows with Google SecOps and Datadog Observability Pipelines
As security threats increase in complexity and scale, modern SIEM solutions are becoming key choices by CISOs for consolidating security monitoring and incident response. Organizations relying on Google or Google Cloud infrastructure are increasingly adopting Google Security Operations (SecOps) to unify their security stack and workflows.